
Manufacturing Identity Governance: The Identity Risk Organizations Are Not Governing
Walk through the access governance of a typical mid-sized manufacturer and a pattern becomes visible quickly. Emplo

Walk through the access governance of a typical mid-sized manufacturer and a pattern becomes visible quickly. Emplo

Most organizations design identity governance programs to be consistent. They apply the same review cycles across s

Across regulated industries, identity governance programs often evolve under the shadow of audit preparation. Acces
Why Identity Governance Risk Starts With How Access Decisions Are Made Identity governance risk is not always visib
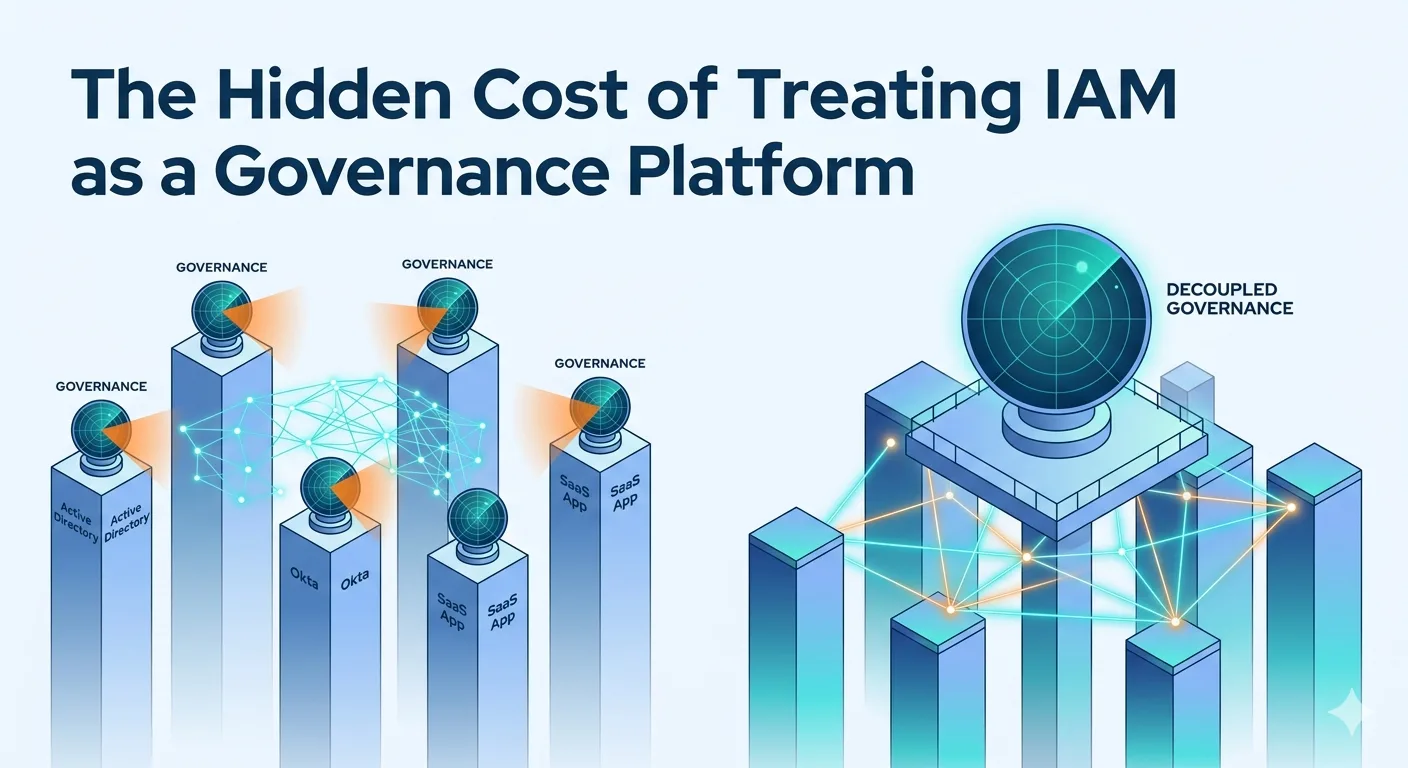
There is a quiet assumption embedded in how many enterprises approach identity security governance: that because IAM sys
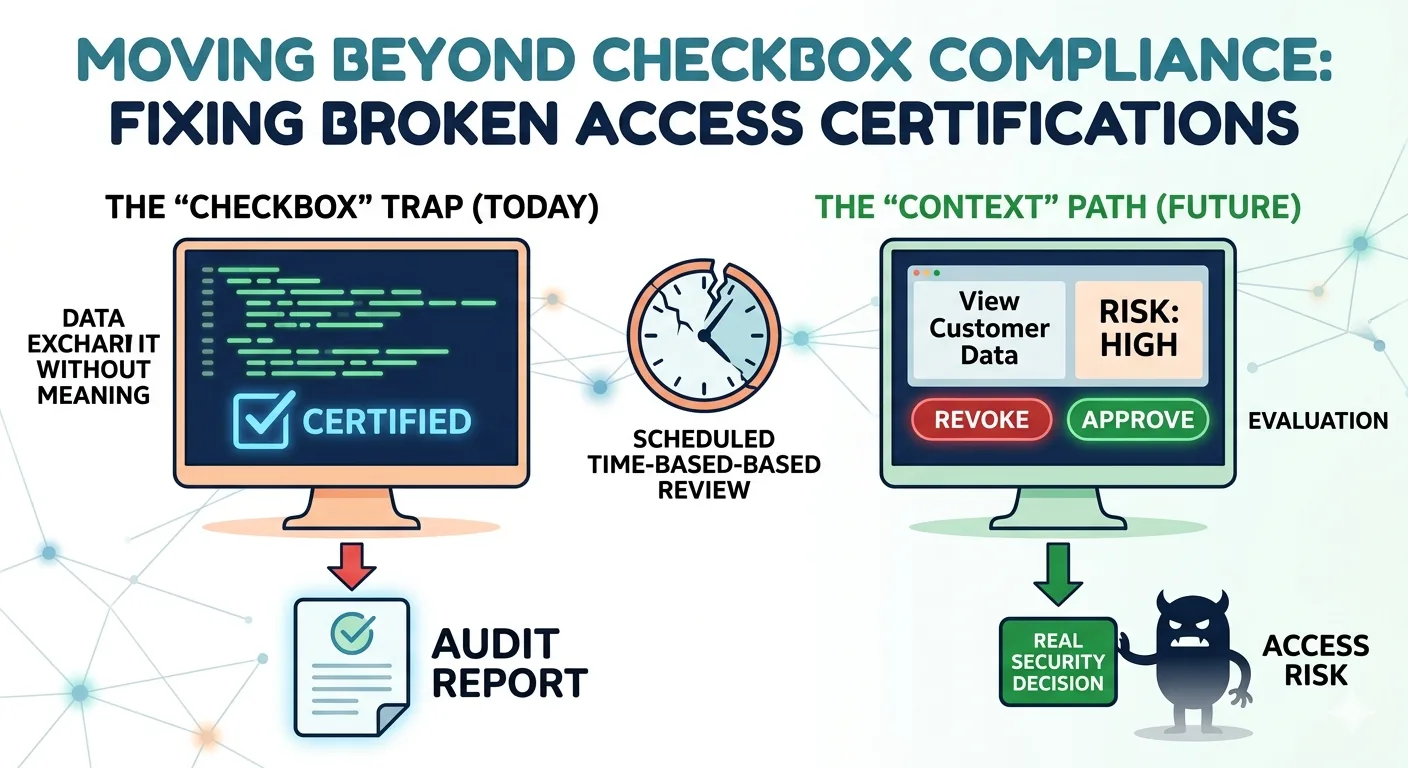
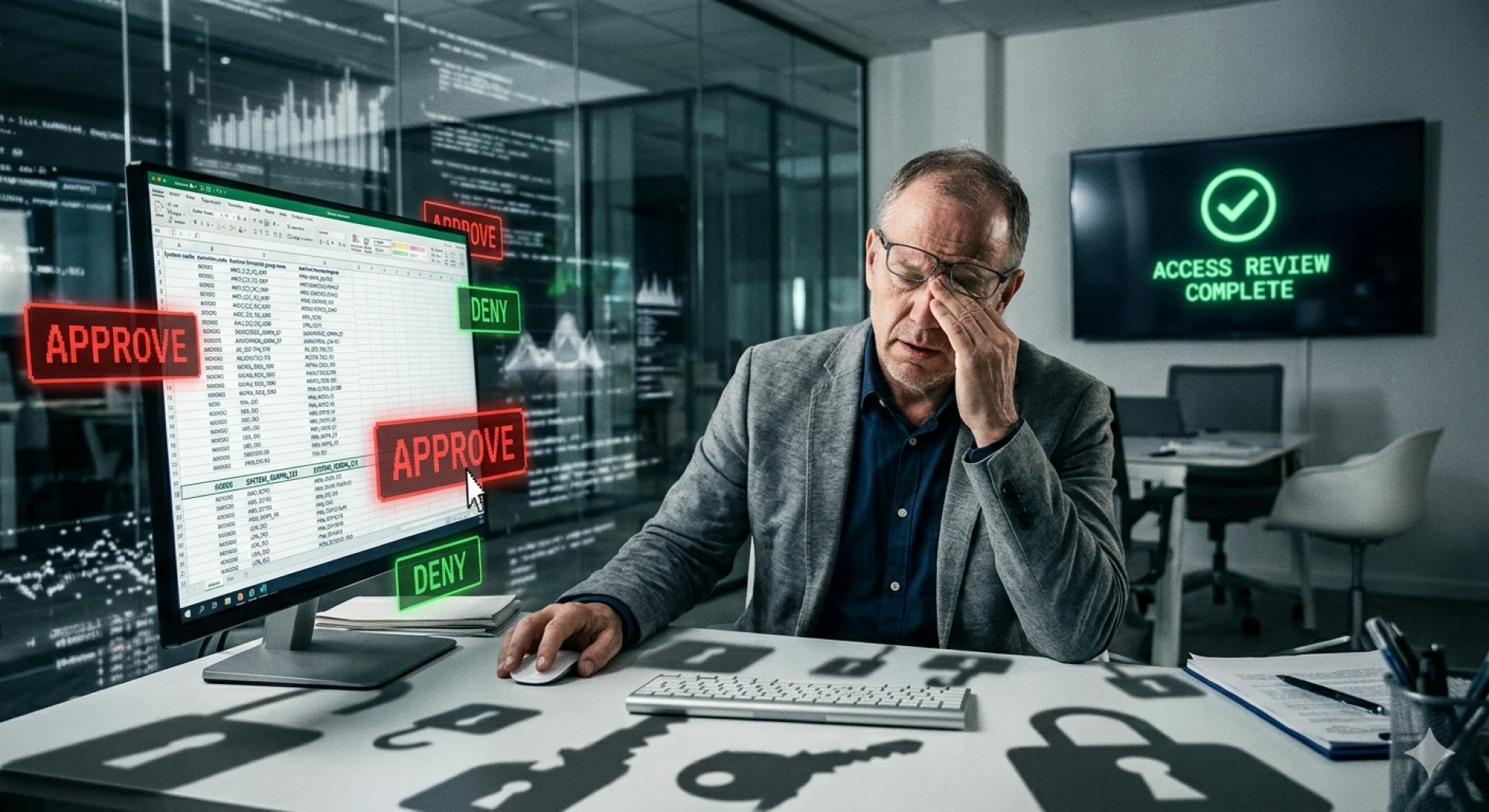
What Actually Breaks Access Certification Programs (It's Not What You Think) Most organizations running access cert
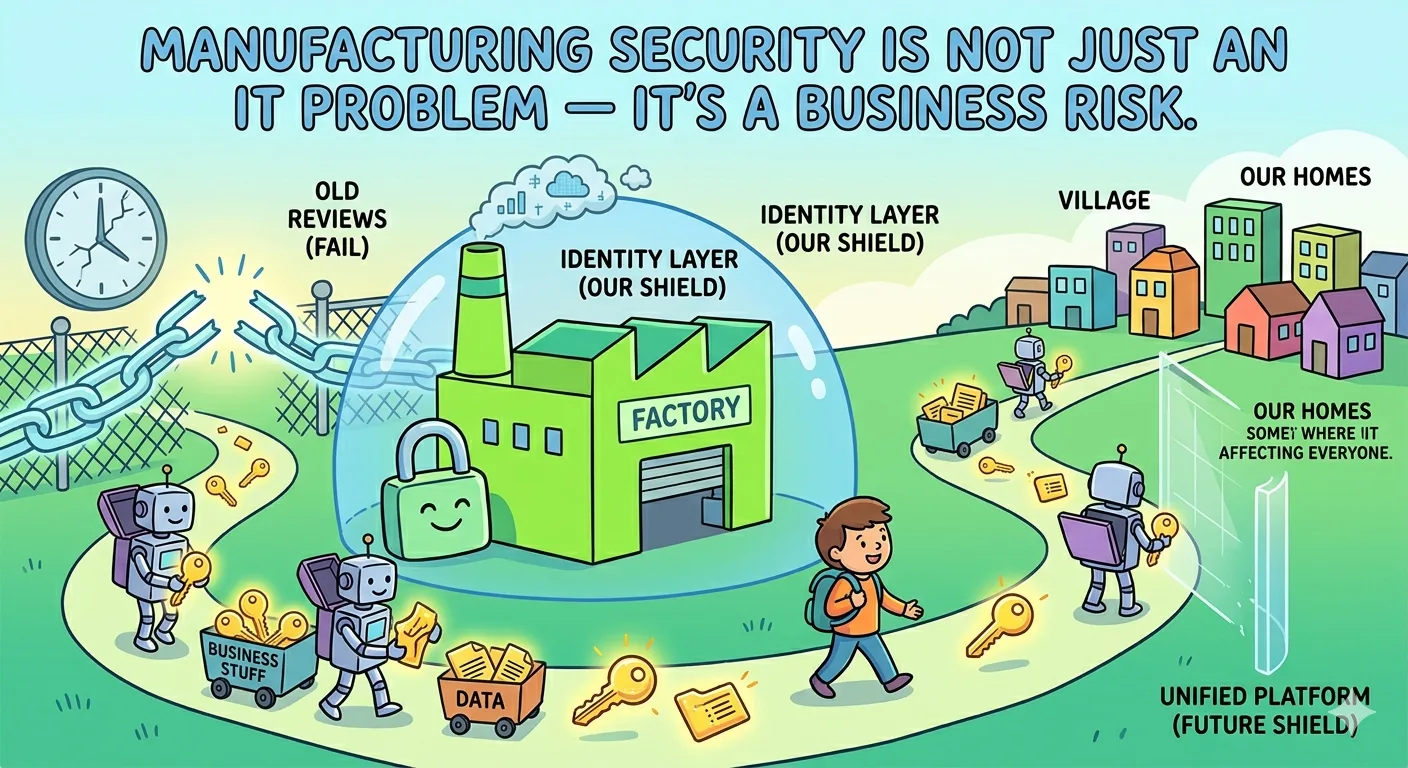
Manufacturing has become the most targeted industry for cyberattacks. And in the vast majority of incidents, the entry p
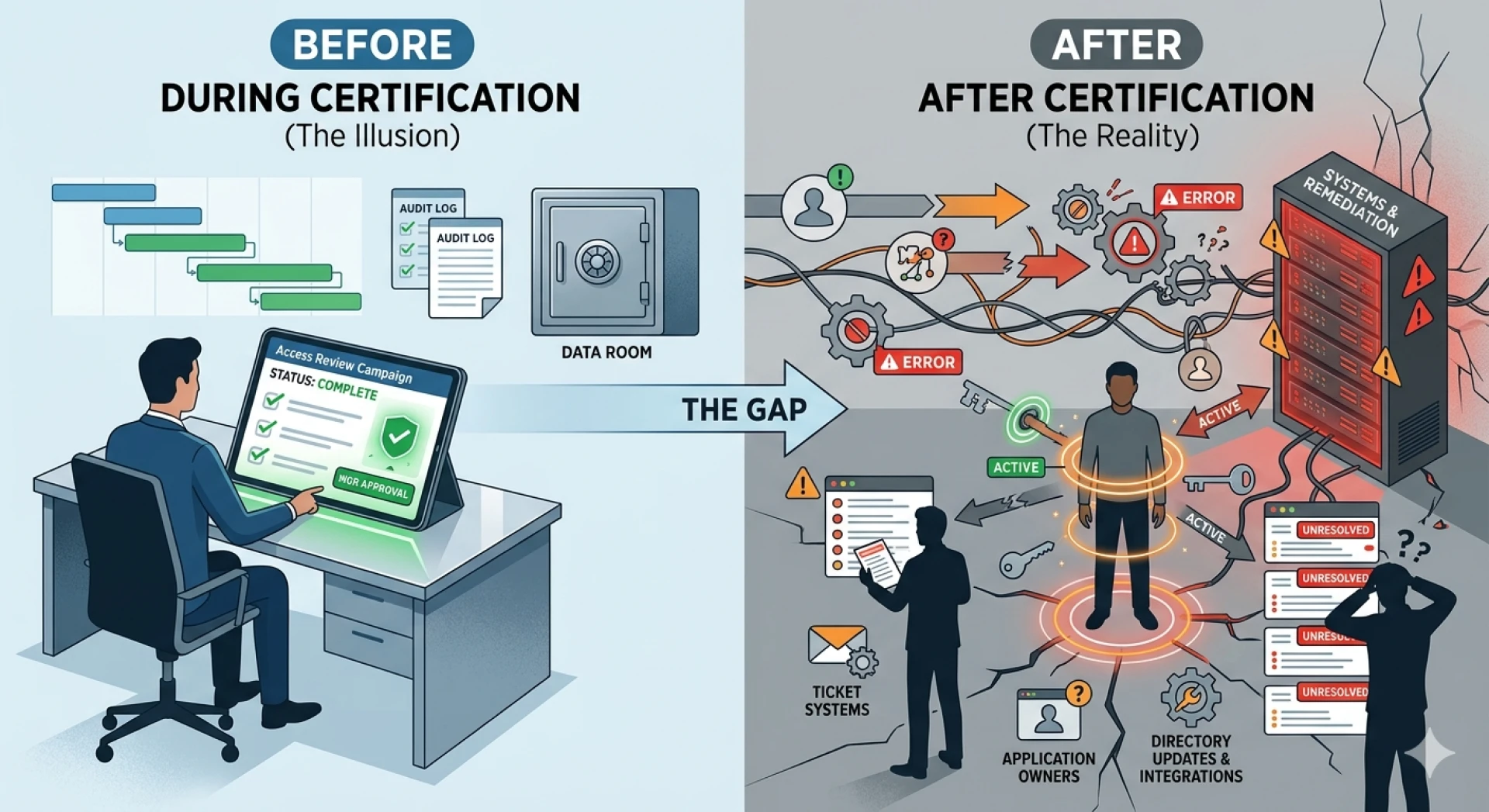
A split-screen illustration titled 'Before vs After Certification.' The left side shows a clean 'Complete' status on an
Why Your Access Review Is Lying to You (& How SaaS Made It Worse)

The Modernization Assumption: Why Your IGA Program is Stalling

Is "Access Review Fatigue" Killing Your Governance Program? The Design Fix
Is your IGA program reducing risk or just passing audits? Discover why identity governance often becomes a "compliance r