Manufacturing has become the most targeted industry for cyberattacks. And in the vast majority of incidents, the entry point is not a vulnerability in production systems or operational technology. It is an identity.
Compromised credentials, unrevoked supplier accounts, excessive contractor access — these are the attack surfaces that adversaries are exploiting in industrial environments. For CISOs in manufacturing, this makes manufacturing identity security one of the most consequential areas of the security program.
Why Manufacturing Identity Risk Is Different
Most enterprise identity security frameworks were built around a relatively contained population: employees accessing corporate systems from managed devices on known networks.
Manufacturing environments look nothing like that.
Industrial organizations operate complex ecosystems of internal employees, plant operators, engineering contractors, logistics providers, component suppliers, and service partners — all interacting with enterprise systems that span ERP platforms, manufacturing execution systems, product lifecycle environments, and supply chain portals.
Each of these populations has different access requirements, different risk profiles, and different lifecycle patterns. A supplier engineer onboarded to a SAP portal for a specific project is not the same as a permanent employee. But in many organizations, their identities are managed — or rather, not managed — in exactly the same fragmented, manual way.
This is where manufacturing identity security breaks down. Not at the perimeter. Inside it.
The Supply Chain Identity Governance Gap
Supply chain identity governance is one of the most consistently underdeveloped controls in industrial security.
Suppliers and partners frequently require access to sensitive enterprise systems — supplier portals, quality management platforms, engineering collaboration environments, logistics coordination systems. In many organizations, this access is provisioned manually, governed inconsistently, and rarely reviewed after initial setup.
The result is predictable: accounts accumulate. Supplier personnel change. Projects end. But access remains — sometimes for months or years after the business relationship that justified it has concluded.
This is not a theoretical risk. It is an active exposure. And at the scale of a modern industrial supplier network, it is one that grows with every new partnership, every new project, and every new system integration.
For CISOs, the question is not whether supplier access creates risk. It does. The question is whether the identity governance framework extends far enough to govern it.
Workforce Identity Is the Foundation — But Not the Finish Line
Many industrial organizations have made meaningful progress on workforce identity governance. Lifecycle automation for employees, role-based provisioning, access certification processes — these controls are increasingly in place.
But workforce identity is the foundation, not the complete picture.
As manufacturing operations become more digital and more interconnected, the identity surface extends well beyond internal employees. Contractors require temporary access to production systems. Engineering partners collaborate on sensitive IP environments. Logistics providers connect directly to supply chain platforms. Each of these external participants is a potential entry point — and each requires the same lifecycle discipline applied to permanent employees.
Organizations that treat workforce identity and external identity as separate problems — managed by separate tools with separate policies — introduce the fragmentation that adversaries exploit.
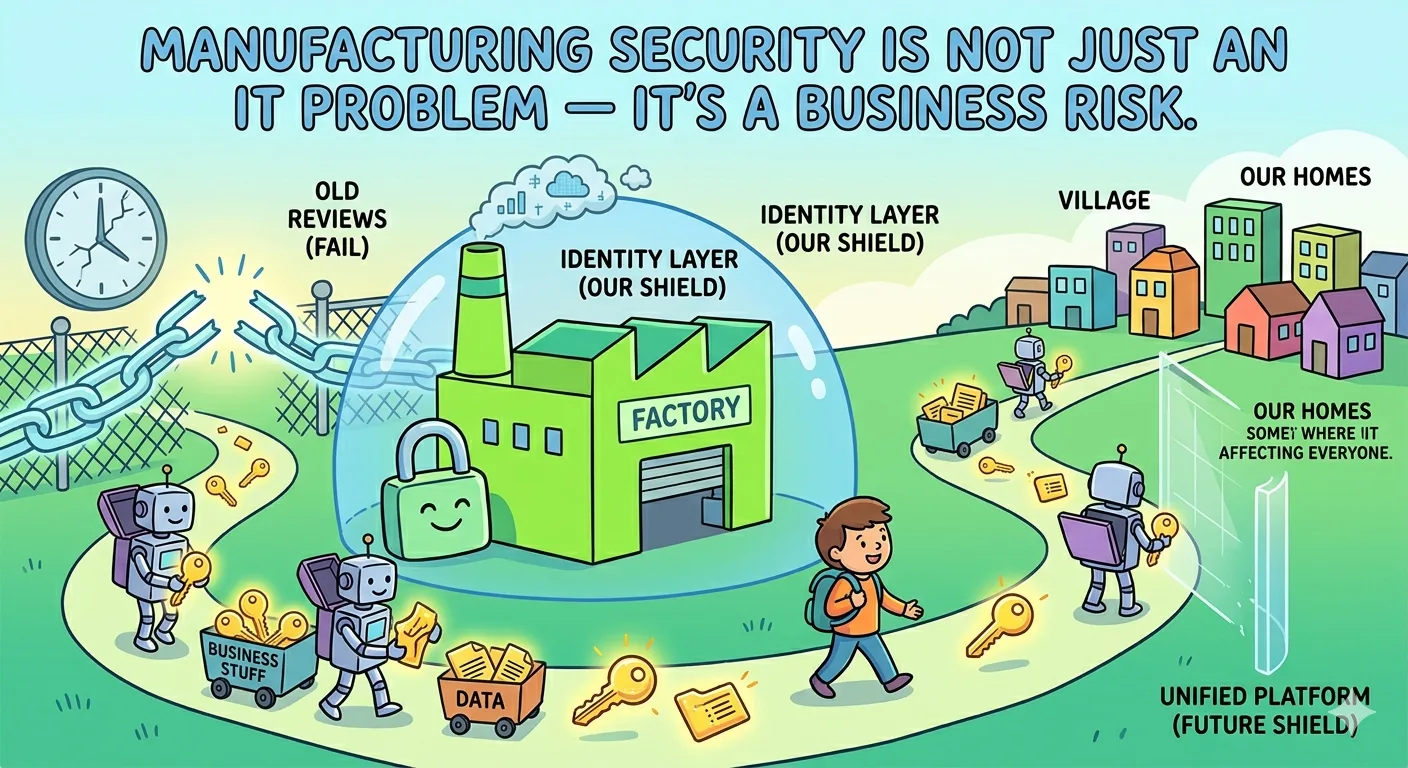
The Strategic Case for a Unified Identity Platform
For CISOs making the case for identity investment in manufacturing environments, the strategic argument is straightforward.
A unified identity governance platform — one that manages workforce access, supplier collaboration, and partner identity under a single policy framework — reduces the attack surface by closing the lifecycle gaps that fragmented tools leave open. It improves audit visibility by providing a consistent record of who has access to what, and why. And it reduces operational overhead by eliminating the manual processes that slow provisioning and delay deprovisioning.
Manufacturing identity security is not a feature request from IT. It is a governance imperative for organizations operating in an environment where identity is the primary attack vector and the supply chain is a primary target.
Conclusion: Identity Is the Control Plane for Industrial Security
Manufacturing organizations today operate across deeply interconnected digital ecosystems. The perimeter is not the factory wall. It is the identity layer that governs who can access enterprise systems — and under what conditions.
CISOs who treat manufacturing identity security as a strategic control layer, rather than an operational function, are better positioned to reduce risk, support compliance, and protect the ecosystems their organizations depend on.
For a detailed look at how identity governance applies across workforce, supplier, and partner ecosystems in manufacturing, see: Identity in Industrial Ecosystems: Securing Workforce, Suppliers, and Partners.