There is a quiet assumption embedded in how many enterprises approach identity security governance: that because IAM systems manage access, they can also govern it. It is an assumption that makes operational sense on the surface. But in practice, it produces governance programs that look functional until they are tested — and fail when it matters most.
Understanding why requires looking at what IAM platforms were actually designed to do, and where that design creates limits for governance.
IAM Was Built for Enforcement, Not Oversight
IAM platforms are transactional systems. Their core function is resolving access decisions in real time: authenticating an identity, evaluating a policy, and allowing or denying a request. They are optimized for speed, consistency, and reliability within the environments they manage.
Identity security governance is a different kind of function. It is not transactional — it is evaluative. It asks not whether access was granted, but whether it should have been. Not whether a policy was enforced, but whether the policy reflects the organization's actual risk posture. Not whether an account exists, but whether the access attached to that account remains appropriate given changes in role, responsibility, and business context.
These are oversight functions. They require the ability to look across the identity estate — not just within a single enforcement layer — and make judgments about access that go beyond what the IAM system's data model was built to support.
The Governance Gap No One Is Auditing
Here is a practical scenario that illustrates the problem. An enterprise runs an access certification campaign using governance tools built into their IAM platform. Reviewers evaluate entitlements for the identities the IAM system manages. The campaign completes. Certifications are logged.
But the enterprise also has dozens of SaaS applications managing their own user access, cloud environments with native identity controls, and a privileged access management system operating independently. None of these are within the IAM platform's governance scope. The access they contain — which may include some of the most sensitive entitlements in the organization — was not evaluated.
The audit report shows a completed certification cycle. The actual access risk in the environment has not changed.
This is the IAM governance gap: governance that appears complete because the IAM system has no visibility into what it is missing.
Risk Does Not Respect System Boundaries
A related problem is that access risk is rarely contained within a single system's data model. The most significant access risk scenarios in enterprise environments typically involve combinations — an account with administrative access in one system and financial transaction authority in another, or an identity with broad read permissions across cloud storage combined with the ability to export that data through an unmanaged SaaS tool.
IAM-native governance evaluates access risk using the constructs available within the IAM platform. It can identify that a role has excessive permissions within the systems it manages. It cannot easily evaluate the combination of entitlements across systems it does not manage.
Effective access risk management requires the ability to reason about identity and access holistically — across all systems, not just those visible to a single IAM platform. When governance logic is housed inside IAM infrastructure, that holistic view is structurally unavailable.
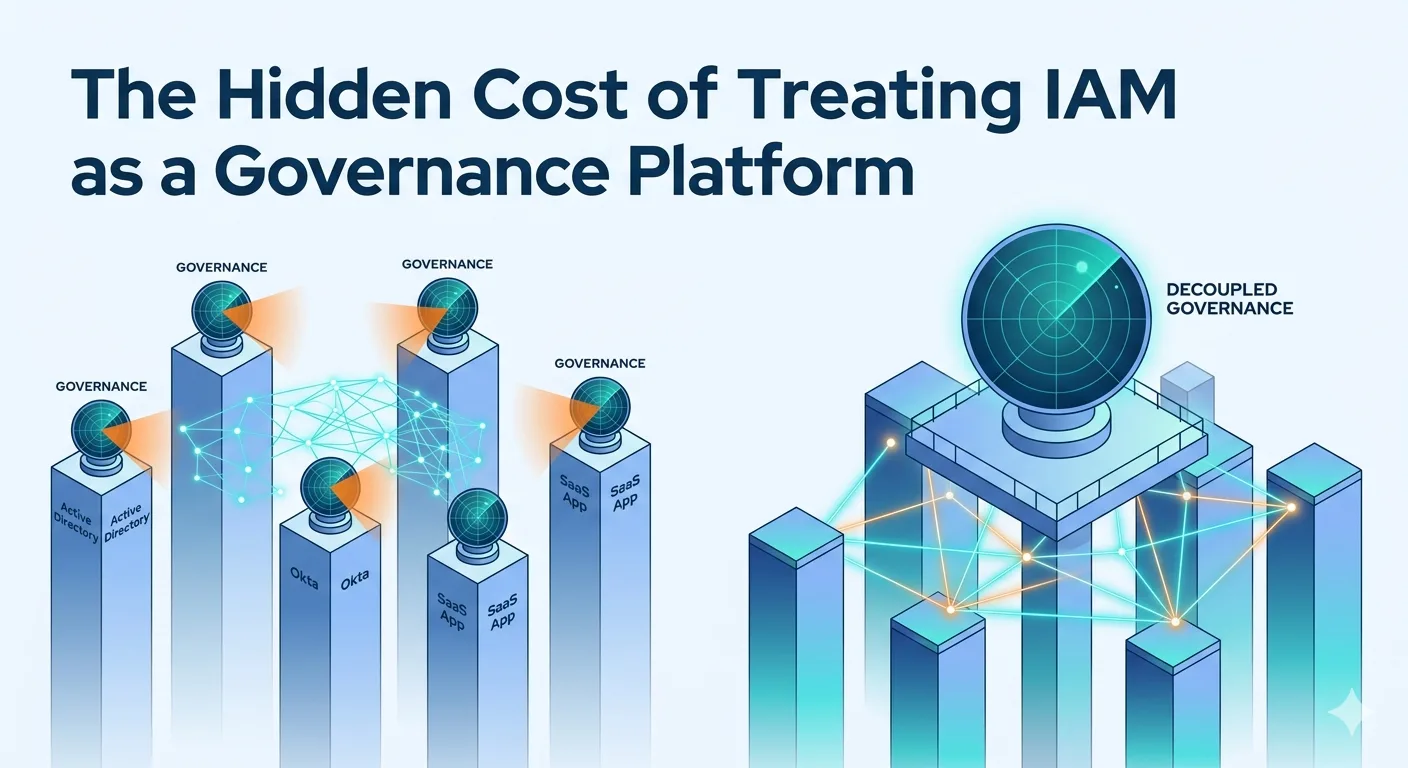
Decoupled Governance Changes the Equation
The enterprises moving beyond this limitation are separating the governance function from the enforcement function — not by removing IAM, but by ensuring governance is not architecturally dependent on it.
A decoupled identity governance layer operates independently of any specific IAM system. It ingests identity and access data from across the enterprise environment — multiple IAM platforms, cloud identity providers, SaaS systems, directories — and applies governance logic that is not constrained by any single system's data model or integration scope.
This architecture does not require replacing IAM investments. IAM platforms continue to enforce access. The governance layer evaluates, validates, and controls that access from a position that is not bounded by any single enforcement system's visibility or capabilities.
The result is governance that reflects the actual state of enterprise access — not just the portion of it that one IAM platform can see.
The Cost of the Assumption
The hidden cost of treating IAM as a governance platform is not always visible in day-to-day operations. It shows up in audit findings that reveal access no certification process reviewed, in incidents involving entitlements that governance never evaluated, and in compliance gaps that existed undetected in the space between IAM systems.
Recognizing that IAM and governance are distinct architectural functions is the first step toward closing those gaps.