Overview
The connected banking system is growing rapidly. This brings both opportunity and responsibility. Therefore, choosing the right IoT app development company is important. This decision can determine whether your innovation is secure or exposed.
While connected systems can enhance efficiency and improve the customer experience, they also require robust IoT security and well-defined data protection strategies. When security and compliance are built into the foundation from day one, scaling becomes far more confident and controlled.
This post discusses what secure IoT adoption looks like for financial institutions and how to implement it effectively using strong data protection strategies. First, we will examine the risks and challenges currently shaping IoT security in the banking sector.
Why IoT Security in Banking Is Now a Board-Level Concern
In banking, IoT security is all about keeping connected devices, networks, and applications safe from cyber attacks, data breaches, and operational disruptions. Unlike traditional systems, IoT setups span everything at once- from devices and cloud platforms to APIs and core banking systems- making the environment far more interconnected. And that’s exactly what makes them so complex.
Here’s what increases the risk-
- Multiple connected endpoints
- Real-time data transmission
- Third-party integrations
- Remote device management
- Legacy banking infrastructure integration
Each device becomes connected to a wider digital network. If just one endpoint is breached, it can trigger a chain reaction. This can put customer data, transaction accuracy, and compliance requirements at risk.
Financial institutions must adhere to regulations such as PCI DSS, ISO 27001, SOC 2, and regional data protection laws. Even a single weak point in an IoT device can result in heavy penalties, system disruptions, and place your brand’s reputation at stake.
We have understood why the risks are higher. So, the next step is choosing the right partner to design and protect your connected ecosystem.
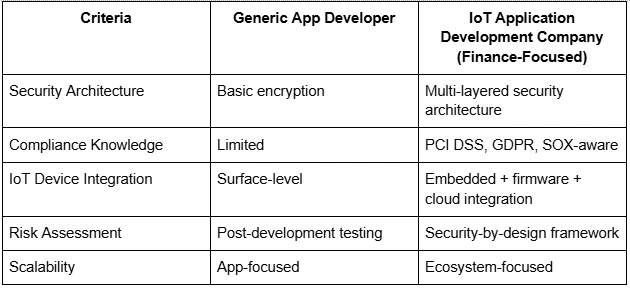
Generic Developers vs. a Specialized IoT App Development Company
Every development partner cannot handle the level of security that financial systems require. This is where many organizations make heavy mistakes.
A standard development company can build a connected app. However, a seasoned IoT application development company possesses expertise in everything, from hardware and firmware to connectivity, cloud architecture, and regulatory compliance.
Here are the practical differences between the two developers.
Generic App Developer
- Focuses primarily on app functionality
- Adds security features after development
- Limited experience with embedded systems
- Basic encryption and authentication
- Reactive testing approach
Specialized IoT App Development Company
- Design security into the architecture from day one
- Understands device-level vulnerabilities
- Implements end-to-end encryption
- Builds compliance-ready frameworks
- Uses proactive threat modeling
Besides protecting a mobile interface, IoT security in financial services has multiple layers of protection, including device authentication protocols, secure firmware updates, and zero-trust network models. Data must be encrypted both at rest and in transit. Real-time monitoring and audit logging can detect any suspicious activity and address it immediately.
In financial environments, security cannot be an add-on. It must be embedded into the very foundation.
Next, we will take a look at implementing the IoT systems the right way.
Implementing IoT Data Protection Strategies That Actually Work
Security starts at the architecture level. Strong IoT data protection strategies prevent vulnerabilities before they become threats. Let's jump into these strategies.
Secure Architecture Design
The starting point for any secure IoT system lies in a strong structure. A well-designed framework comprises edge-to-cloud encryption, secure boot mechanisms, hardware-based key storage, network segmentation, and API gateway protection. It keeps the entire ecosystem protected from end to end.
Secure boot, for example, makes sure each device only runs trusted software, keeping the system safe from tampering. Network segmentation prevents attackers from moving freely across systems. These measures form the foundation of security; they are not optional upgrades.
Identity and Access Management (IAM)
Every connected device has its own unique identity. Without proper authentication, devices can be impersonated or taken over.
Strong IoT security in banking involves certificate-based device authentication, role-based access control, automated credential rotation, and multi-factor authentication for administrators.
Identity management is about users and also ensures devices can communicate with each other safely and securely.
Continuous Monitoring and Threat Detection
Relying on static security measures is not enough anymore. Continuous monitoring is essential. Anomaly detection systems track device behavior and flag any unusual activity. For example, if a POS device suddenly sends an unexpected amount of data, the system triggers alerts.
Today’s IoT ecosystems use AI-driven monitoring, real-time threat intelligence, behavioral analytics, and automated response workflows. This approach makes security proactive and adaptive, rather than simply reacting after a problem occurs.
Compliance Built Into the System
Regulatory requirements must assist development at the outset. It is not something that can be addressed at the final stage.
A company that is into IoT app development ensures your system includes encrypted transaction logs, audit-ready reporting, secure API documentation, and regular penetration testing. When compliance is integrated from the beginning, audits feel manageable rather than overwhelming.
We will now delve into how your IoT ecosystem can scale safely.
Scaling Secure IoT in Financial Services Without Increasing Risk
As financial institutions expand their IoT networks, they add more devices, more integrations, and more data streams. If strong IoT data protection strategies do not exist, then new challenges will emerge. That is why the goal should be towards scalable security.
Modular and Microservices Architecture
Scalable IoT systems depend on a modular design. Instead of building one large, tightly connected system, secure setups break things into smaller, manageable parts. They use microservices-based architecture, API gateways, containerized deployments, and automated patch updates to keep everything flexible and secure. This way, you can update or fix one part of the system without affecting everything else.
Automated Patch and Firmware Management
Outdated firmware is one of the easiest ways for attackers to exploit a system. An experienced IoT app development company set up automated update pipelines to provide secure over-the-air firmware updates, validate patches before deployment, and offer rollback options if something goes wrong. This approach minimizes human error and reduces the time devices remain vulnerable.
Predictive Security Models
The future of IoT security in financial services is moving toward predictive protection. More organizations rely on risk scoring engines, predictive analytics, AI-driven vulnerability detection, and automated compliance checks. Rather than reacting to threats after they occur, these systems spot patterns that signal potential risks ahead of time. Security is shifting from a reactive defense to proactive foresight.
Data Governance as a Strategic Asset
Effective IoT data protection does not just prevent risks. It also adds business value. When data is properly organized and securely managed, it boosts customer trust, improves operational efficiency, speeds up fraud detection, and makes audits more transparent. In this way, strong security gives a competitive edge. It is not just a regulatory requirement.
Concluding Remarks
In banking, the stakes are always high. Choosing the right IoT app development company plays a critical role in ensuring your connected systems strengthen your operations rather than expose them to risk. Simply put, safeguarding trust matters as much as driving innovations.




