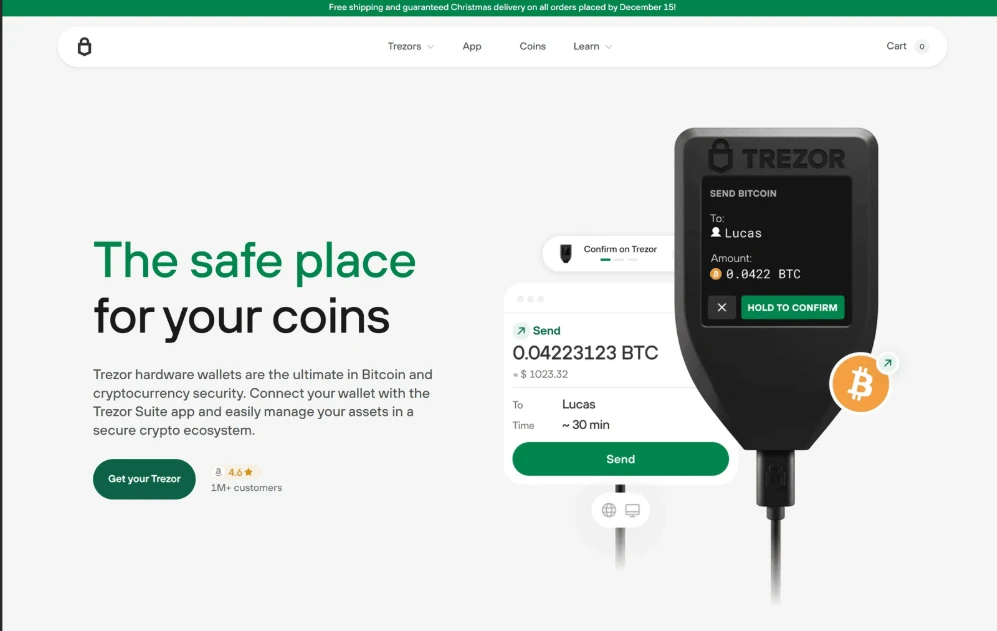
In the evolving world of cryptocurrency, secure access to digital assets is more important than ever. One essential tool that enhances both security and usability for hardware wallet users is Trezor Bridge. Designed to act as a communication layer between your browser and your Trezor device, Trezor Bridge simplifies the login process while maintaining top-tier protection for your funds.
What is Trezor Bridge?
Trezor Bridge is a lightweight software that enables smooth interaction between your computer and your Trezor hardware wallet. Unlike traditional browser extensions, it runs quietly in the background and ensures your browser can securely communicate with your device. When you initiate a login through the Trezor Suite or supported platforms, Trezor Bridge ensures that your credentials and approvals are transmitted safely without exposing sensitive information.
How Trezor Bridge Login Works
The login process using Trezor Bridge is both simple and secure. Once installed, the software automatically detects your connected Trezor device. When you attempt to log in to your wallet interface, you are prompted to confirm the action physically on your device. This extra step ensures that no unauthorized access can occur, even if your computer is compromised.
Unlike password-based logins, Trezor Bridge relies on cryptographic authentication. This means your private keys never leave your device, and every login request must be manually approved. This approach significantly reduces the risk of phishing attacks and data breaches.
Advantages of Trezor Bridge Login
One of the biggest advantages of Trezor Bridge is its enhanced security model. By eliminating the need to input sensitive credentials on your computer, it protects users from keyloggers and malicious software. Additionally, the direct communication between the device and browser ensures a seamless and reliable connection.
Another advantage is compatibility. Trezor Bridge supports multiple browsers and operating systems, making it accessible for a wide range of users. It also receives regular updates, ensuring that security standards remain up to date with the latest threats in the crypto space.
Key Benefits for Users
Trezor Bridge offers several practical benefits that make it a preferred choice among crypto enthusiasts. First, it provides a user-friendly experience. Even beginners can easily install and use the software without technical knowledge. The automatic detection feature saves time and eliminates complex setup procedures.
Second, it enhances transaction verification. Every login and transaction must be confirmed on the hardware wallet, giving users full control over their assets. This reduces the chances of accidental or unauthorized actions.
Lastly, it ensures privacy. Since no sensitive data is stored on external servers or browsers, users maintain complete ownership of their information. This aligns perfectly with the decentralized philosophy of cryptocurrency.
Final Thoughts
Trezor Bridge login stands out as a powerful and secure solution for accessing your crypto wallet. It combines simplicity with advanced protection, making it suitable for both beginners and experienced users. By acting as a secure bridge between your device and browser, it ensures that your digital assets remain safe at all times.
In a world where cyber threats are constantly evolving, using tools like Trezor Bridge is not just an option—it’s a necessity. If you value security, privacy, and ease of use, Trezor Bridge delivers an amazing and reliable experience that truly elevates your crypto journey.