Cryptocurrency exchanges are at the heart of the digital asset ecosystem, enabling users to buy, sell, and trade cryptocurrencies seamlessly. However, their growing popularity has made them prime targets for cyberattacks, hacks, and data breaches.
Unlike traditional financial systems, crypto transactions are irreversible. This means even a minor security flaw can lead to massive financial losses and reputational damage. For any business planning to build or operate a crypto exchange, implementing a strong security framework is not optional—it is essential.
Understanding the Threat Landscape
Crypto exchanges face a wide range of security threats, including:
- External hacking attempts targeting wallets and servers
- Phishing and social engineering attacks on users
- Smart contract vulnerabilities in decentralized systems
- Insider threats from employees or stakeholders
- API exploitation and DDoS attacks
These threats are constantly evolving, requiring exchanges to adopt proactive and multi-layered security strategies.
Core Components of a Strong Security Framework
To protect a cryptocurrency exchange effectively, businesses must implement a comprehensive security architecture that addresses all potential vulnerabilities.
1. Secure Wallet Management
Wallets are the most critical component of any crypto exchange.
Best Practices:
- Use cold wallets for storing the majority of funds offline
- Maintain hot wallets only for active transactions
- Implement multi-signature (multi-sig) wallets
- Use Multi-Party Computation (MPC) for key management
Outcome:
Minimized risk of unauthorized access and fund theft.
2. Strong User Authentication Mechanisms
User accounts are often the weakest link in security.
Key Features:
- Two-Factor Authentication (2FA)
- Biometric authentication (fingerprint/face ID)
- Anti-phishing codes
- Session and device management
Benefit:
Prevents unauthorized account access and enhances user trust.
3. Advanced Encryption Protocols
Data protection is crucial for both user information and transactions.
Implementation:
- End-to-end encryption
- SSL/TLS protocols for secure communication
- Encryption of sensitive data at rest and in transit
Result:
Protection against data breaches and interception attacks.
4. Secure API Infrastructure
APIs connect exchanges with external services, making them potential entry points for attackers.
Best Practices:
- Use API key authentication
- Implement rate limiting and IP whitelisting
- Encrypt API communications
- Regularly audit API endpoints
Outcome:
Reduced risk of unauthorized access and data manipulation.
5. Real-Time Monitoring and Threat Detection
Continuous monitoring is essential to detect suspicious activities.
Tools & Techniques:
- AI-based anomaly detection
- Real-time transaction monitoring
- Automated alerts and incident response systems
Benefit:
Quick identification and mitigation of threats before they escalate.
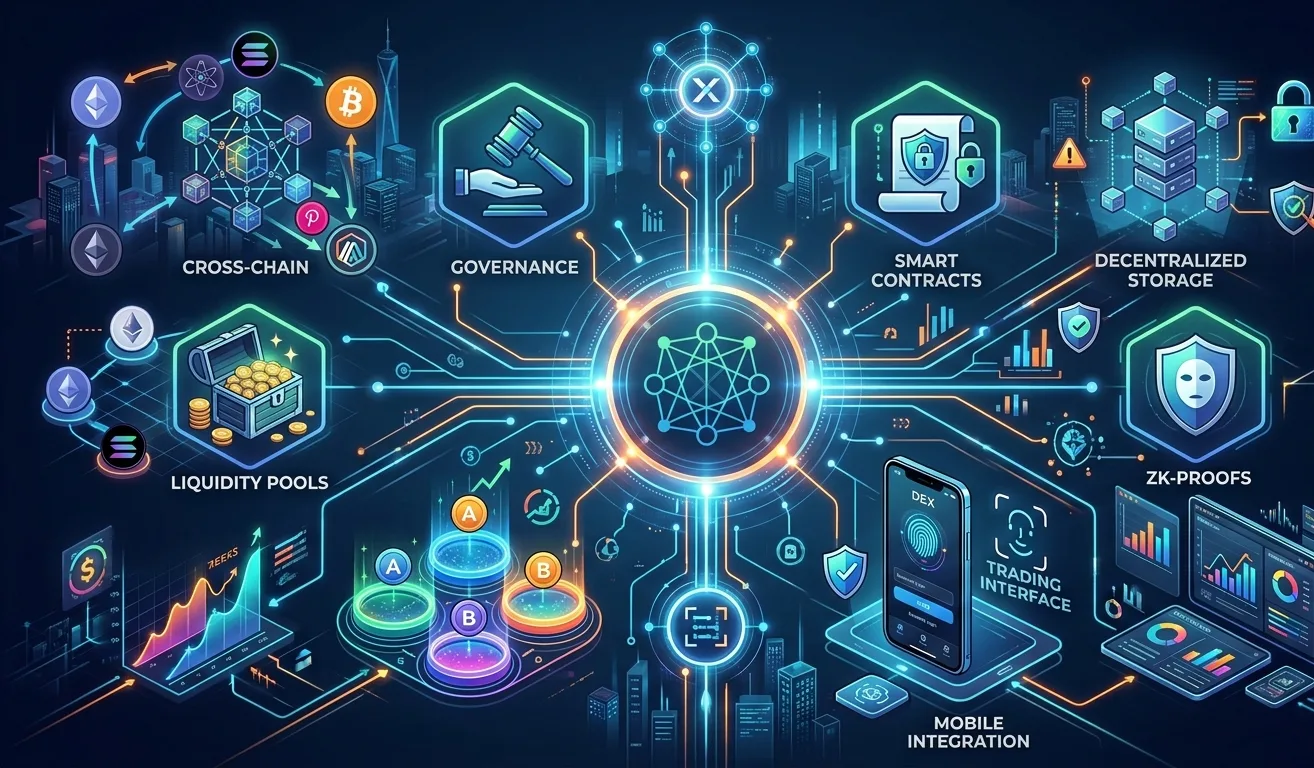
6. Smart Contract Security (For DEX Platforms)
For decentralized exchanges, smart contracts play a key role.
Risks Include:
- Reentrancy attacks
- Logic errors
- Code vulnerabilities
Mitigation:
- Conduct third-party smart contract audits
- Use verified libraries
- Perform extensive testing
7. DDoS Protection and Infrastructure Security
Distributed Denial of Service (DDoS) attacks can disrupt exchange operations.
Preventive Measures:
- Use cloud-based DDoS protection services
- Implement load balancing
- Maintain redundant servers
Result:
Ensures platform availability and performance.
8. Regulatory Compliance and KYC/AML Integration
Compliance plays a key role in security and trust.
Key Elements:
- KYC (Know Your Customer) verification
- AML (Anti-Money Laundering) monitoring
- Transaction tracking and reporting
Benefit:
Prevents illegal activities and enhances credibility.
9. Internal Security Controls
Not all threats are external—insider risks can be equally damaging.
Best Practices:
- Role-Based Access Control (RBAC)
- Multi-level approval systems
- Employee activity monitoring
- Regular internal audits
Outcome:
Reduced risk of internal misuse or data leaks.
10. Regular Security Audits and Penetration Testing
Security is an ongoing process, not a one-time setup.
Approach:
- Conduct periodic vulnerability assessments
- Perform penetration testing
- Run bug bounty programs
Result:
Continuous improvement and proactive risk mitigation.
Common Mistakes to Avoid
Many exchanges fail due to avoidable security lapses:
- Storing large funds in hot wallets
- Weak password policies
- Lack of monitoring systems
- Ignoring regular updates and patches
- Poor API security
Avoiding these mistakes can significantly strengthen your exchange’s defense.
Role of Advanced Technologies in Exchange Security
Modern technologies are transforming crypto exchange security:
- AI & Machine Learning: Detect fraud and anomalies in real time
- Blockchain Analytics: Track suspicious transactions
- MPC Wallets: Eliminate single points of failure
- Zero-Trust Security Models: Enforce strict access controls
These innovations help exchanges stay ahead of evolving cyber threats.
Dappfort’s Approach to Crypto Exchange Security
Dappfort follows a security-first approach in cryptocurrency exchange development. By combining advanced technologies with industry best practices, the company delivers highly secure and scalable exchange platforms.
Key Highlights:
- Multi-layer security architecture
- Secure wallet and key management
- Real-time monitoring systems
- Compliance-ready solutions
- Regular audits and testing
This ensures that businesses can launch exchanges with confidence and reliability.
Future of Crypto Exchange Security
As the crypto industry evolves, security frameworks will continue to advance.
Emerging Trends:
- AI-driven autonomous security systems
- Decentralized identity verification
- Privacy-enhancing technologies
- Cross-chain security protocols
These innovations will redefine how exchanges protect user assets and data.
Conclusion
Security is the foundation of any successful cryptocurrency exchange. With increasing cyber threats, businesses must adopt a comprehensive and proactive security framework that covers every aspect of the platform—from wallets and APIs to user authentication and compliance.
By implementing best practices and leveraging advanced technologies, exchanges can prevent hacks, mitigate risks, and build trust among users.
Partnering with an experienced development company like Dappfort ensures that your exchange is built with security at its core—ready to handle the challenges of the evolving crypto landscape.