When people learn about crypto security, they often think of technical attacks hacking, malware, and key exposure. There's a more insidious, underappreciated threat, however: social engineering attacks.
Hackers no longer need to break into wallets through brute force; they can simply manipulate users into giving up their access. Even the most secure crypto wallet can’t protect users who fall victim to sophisticated deception tactics. In this article, we’ll explore how social engineering attacks work, real-world cases, and how to safeguard your assets.

What Are Social Engineering Attacks?
Social engineering is a type of psychological manipulation that tricks the user into divulging sensitive information. Instead of exploiting the weaknesses of the software, the attackers exploit the weaknesses of human nature.
Social engineering in the crypto frontier can be achieved in a variety of ways, including:
Impersonation Scams : Phishers posing as customer care agents of reputable wallet providers.
Phishing Attacks : Fake emails, websites, or messages aimed at stealing login credentials and seed phrases.
Baiting & Pretexting : The hackers create fictional scenarios in an effort to gain your trust before requesting sensitive information.
Even the operator of the most secure bitcoin wallet can be caught out if they are unaware of such deception.
Why Social Engineering Compromises Crypto Wallets
Crypto wallets have robust protection, but human vulnerability opens the door to hackers. Here's how it's achieved:
1. Wallet Support Scams
A customer looking for internet wallet support is redirected to a fake customer support telephone number or Twitter handle, where the criminals masquerade as legitimate contacts. The scammer tricks them into "verifying" their wallet by revealing their seed phrase leading to asset loss instantly.
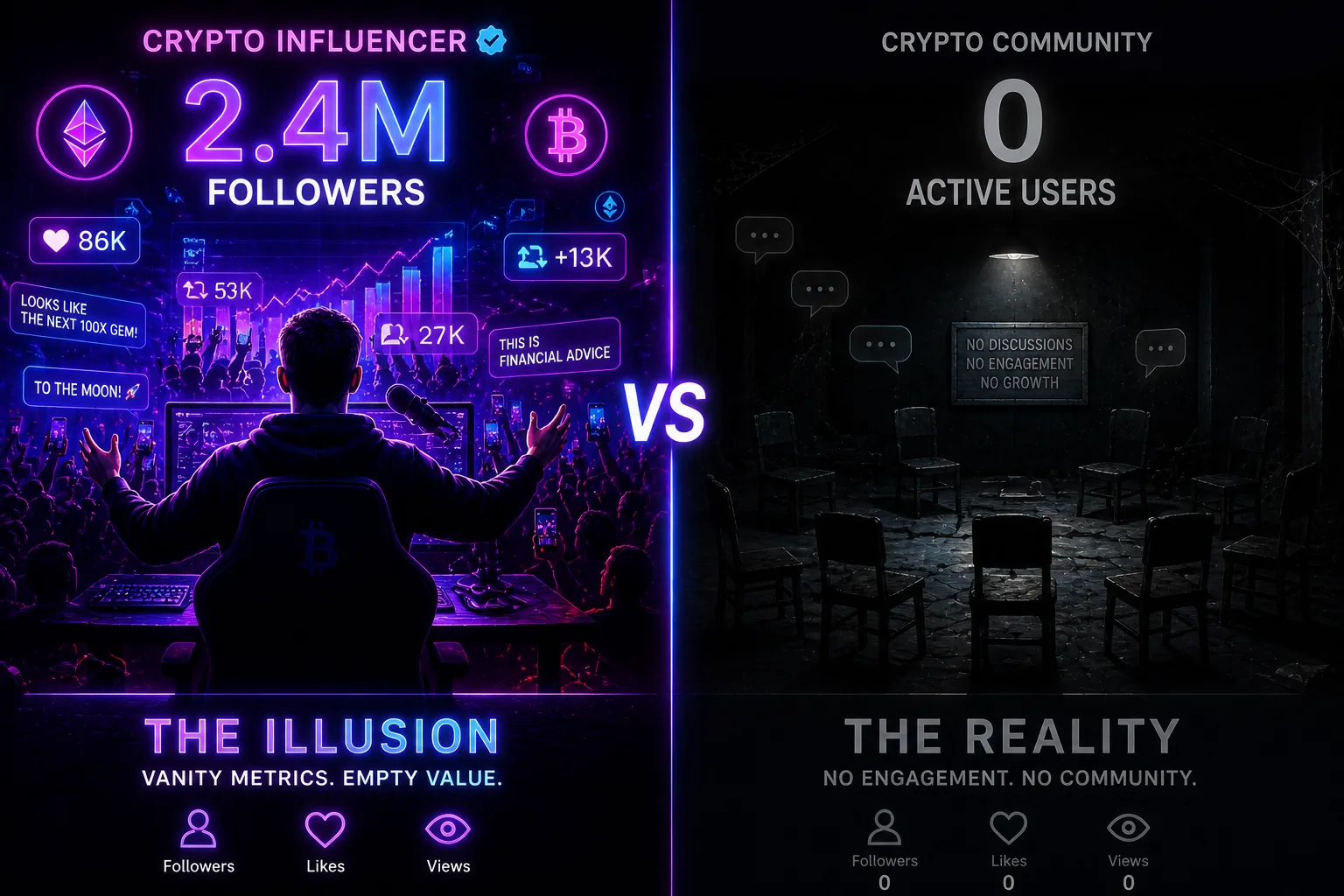
2. Discord & Telegram Scams
Discord and Telegram crypto groups are treasure troves. Hackers masquerade as admins or developers, sending false "wallet updates" or "security updates" which are infected with malware.
3. SIM Swapping Attacks
Hackers socially engineer mobile carriers into porting a victim's phone number to their own phone. They change exchange and wallet passwords after they gain control. Even the owner of the most secure cryptocurrency wallet can be compromised if 2FA is SMS-based.
How to Protect Yourself from Social Engineering Attacks
Since social engineering is all about games of the mind, your best defenses are awareness and watchfulness.
1. Never Give Out Your Seed Phrase
No reputable wallet provider is ever going to request your seed phrase—not by email, phone, or chat. If they do, it's a scam.
2. Use Hardware Wallets with Offline Storage
Hardware wallet is one of the most secure cryptocurrency wallets. Since private keys are always offline, phishing and impersonation scams can't hack them.
3. Enable More Secure 2FA Options
Avoid using SMS 2FA, which is susceptible to hijacking due to SIM-swapping. Instead, use apps like Google Authenticator or security hardware keys.
4. Secure All Support Accounts
Always go to the support site of your wallet vendor prior to contacting support. Refrain from engaging with direct messages from "support agents" on social media platforms.
5. Be Up-to-Date on Popular Scams
Hunters create new techniques minute by minute. Stay updated from credible crypto security forums, blogs, and crypto news websites.
The Future of Cryptocurrency Wallet Security Against Social Engineering
As hard as it is to eradicate social engineering entirely, vendors are embracing new
countermeasures:
AI-driven fraud detection : Sophisticated AI technology will detect attempted phishing and alert customers in real-time.
Transaction confirmation delay : Withdrawal delay provides some wallets as an extra security feature.
Decentralized identity verification : Future wallets will utilize blockchain-based identities that will block impersonation scams.
As attacks evolve, the selection of best bitcoin wallet extends beyond testing standard security measures and research on man-borne attack protection.
Conclusion
Social engineering is probably the most perilous yet underestimated threat of the crypto world. Not even the safest crypto wallet will save users who naively place their faith in their credentials. Vigilance, checking all messages, and the use of hardware wallets is vital to the security of your holdings.