Kubernetes environments are highly dynamic, distributed, and constantly changing. Containers scale automatically, workloads move between nodes, and deployments happen continuously across cloud-native systems. While Kubernetes provides scalability and flexibility, it also introduces a significantly larger attack surface. Vulnerabilities, misconfigurations, runtime threats, and policy violations can spread quickly if organizations do not have a structured remediation process in place.
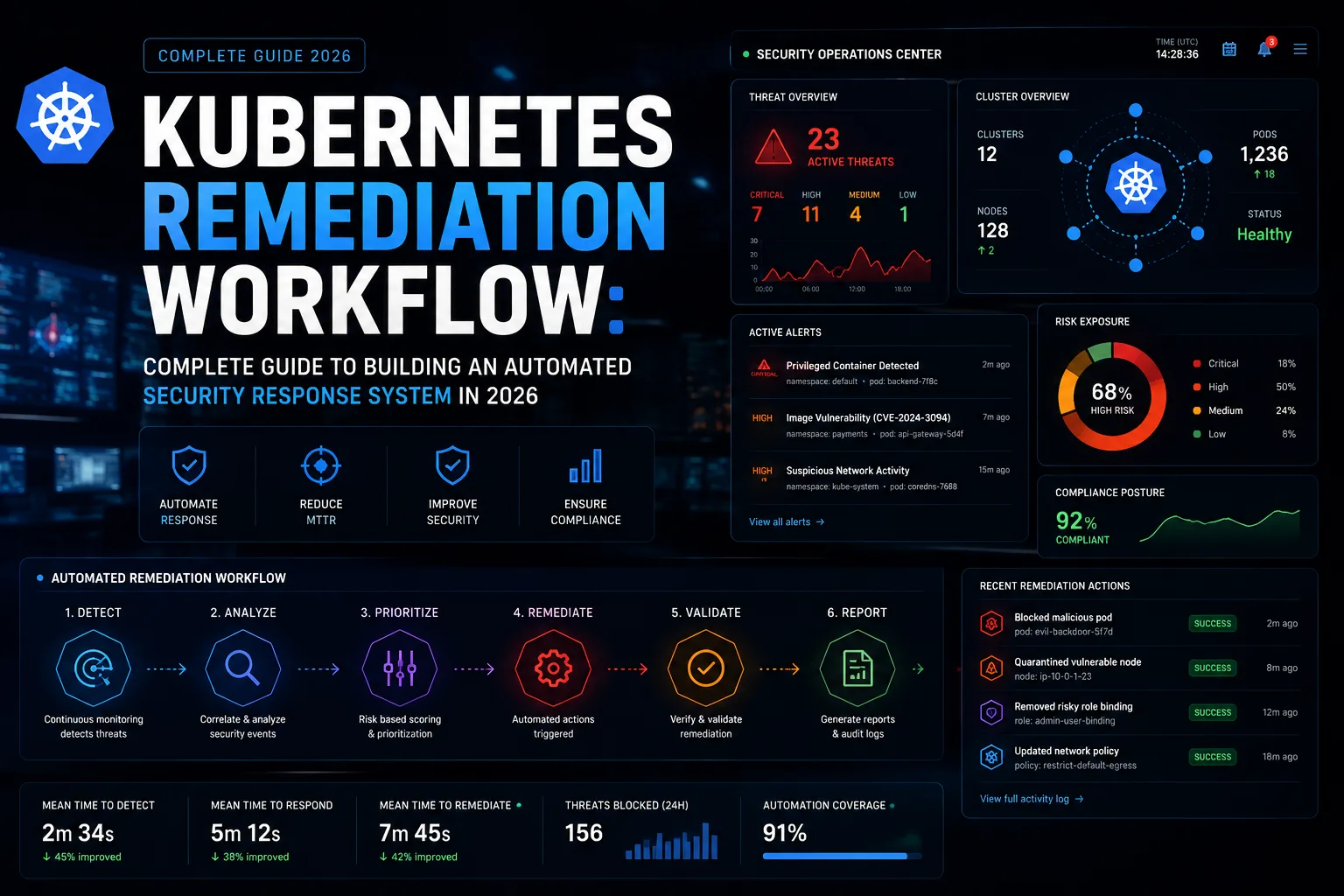
A Kubernetes remediation workflow is a structured process used to identify, prioritize, contain, fix, validate, and continuously monitor vulnerabilities, misconfigurations, and runtime threats across Kubernetes clusters and workloads. It combines automation, DevSecOps practices, runtime monitoring, and policy enforcement to reduce security risks efficiently.
However, many organizations focus only on vulnerability scanning while ignoring remediation orchestration. This creates alert fatigue, delayed responses, and unresolved risks that continue accumulating over time. A modern remediation workflow is not just about finding problems—it is about resolving them continuously and automatically across the entire Kubernetes lifecycle.
In this guide, you will learn how Kubernetes remediation workflows work, the architecture behind them, the tools involved, implementation best practices, automation strategies, and the future of cloud-native security remediation in 2026. Kubernetes has become the industry standard for container orchestration because it automates deployment, scaling, and workload management across complex distributed systems.
Understanding Kubernetes Remediation Workflows and Why They Matter
Kubernetes remediation workflows exist because cloud-native environments are fundamentally different from traditional infrastructure. In legacy systems, security teams could manually investigate vulnerabilities, patch servers individually, and manage infrastructure changes through slower operational cycles. Kubernetes environments operate at a completely different speed and scale.
Containers can be created and destroyed within seconds. New deployments happen multiple times per day, and workloads constantly shift across clusters and cloud environments. This means vulnerabilities can appear, spread, and become exploitable faster than manual security teams can respond.
A Kubernetes remediation workflow provides a structured approach for handling these risks. Instead of relying on isolated security scans, organizations create an automated pipeline that continuously detects threats, prioritizes risks, triggers remediation actions, validates fixes, and monitors workloads after remediation.
Modern remediation workflows typically address several categories of issues:
- Vulnerable container images
- Misconfigured Kubernetes manifests
- Excessive RBAC permissions
- Runtime anomalies
- Exposed secrets
- Insecure network configurations
- Non-compliant workloads
- Supply chain vulnerabilities
- API security issues
One of the biggest challenges in Kubernetes environments is alert overload. Security tools often generate thousands of alerts, many of which are low-risk or non-exploitable. Without prioritization, security teams become overwhelmed and remediation slows significantly.
This is why modern remediation workflows emphasize contextual risk analysis. Organizations must prioritize vulnerabilities based on:
- Runtime exposure
- Public accessibility
- Workload criticality
- Active exploitability
- Business impact
For example, a critical vulnerability inside a publicly exposed workload requires immediate remediation, while the same vulnerability inside an isolated internal development environment may present lower risk.
Another reason remediation workflows are essential is because Kubernetes workloads are deeply interconnected. A single misconfigured service account or overly permissive network policy can create opportunities for attackers to move laterally across the environment. Effective remediation workflows therefore focus on containment as much as patching.
The rise of multi-cloud Kubernetes environments has made remediation even more complex. Organizations now run workloads across AWS, Azure, GCP, and hybrid infrastructure simultaneously. Each cloud provider introduces different IAM systems, APIs, and operational models. This fragmentation makes centralized remediation orchestration increasingly important.
Runtime threats are another major reason remediation workflows have evolved. Traditional vulnerability scanning identifies theoretical risks, but runtime monitoring identifies active threats occurring inside live workloads. Security teams now prioritize runtime-aware remediation because many vulnerabilities only become dangerous when actively exploited.
Modern remediation workflows therefore combine:
- Continuous scanning
- Runtime detection
- Automated policy enforcement
- Infrastructure orchestration
- CI/CD integration
- Centralized observability
This shift reflects a larger transformation in cloud-native security. Organizations are moving from reactive security operations toward automated and continuously adaptive remediation systems.
Core Architecture of an Automated Kubernetes Remediation Workflow
A scalable Kubernetes remediation workflow requires a multi-layered architecture capable of operating continuously across clusters, workloads, and deployment pipelines. Organizations that treat remediation as a disconnected operational process often struggle with inconsistent responses and delayed fixes.
The first layer of the architecture is the detection layer. This layer continuously scans the environment for vulnerabilities, misconfigurations, compliance violations, and runtime threats. Detection systems monitor:
- Container images
- Kubernetes manifests
- Infrastructure-as-code files
- Running workloads
- APIs and ingress traffic
- Network activity
- Cluster configurations
Detection tools must operate continuously because Kubernetes environments change rapidly. Static weekly scans are no longer sufficient in modern cloud-native systems.
The second layer is the analysis and prioritization engine. This layer evaluates detected issues and assigns severity levels based on context. Not all vulnerabilities require the same urgency, so prioritization systems consider factors such as:
- Exposure level
- Internet accessibility
- Runtime activity
- Business criticality
- Existing compensating controls
This contextual analysis reduces alert fatigue and ensures security teams focus on the most exploitable risks first.
The third layer is orchestration and workflow management. This layer coordinates remediation actions across the environment. Depending on the issue type, workflows may include:
- Blocking deployments
- Restarting workloads
- Rolling back deployments
- Applying patches
- Updating configurations
- Revoking credentials
- Isolating workloads
- Scaling down compromised pods
Automation becomes critical at this stage because manual remediation cannot keep pace with Kubernetes deployment velocity.
The fourth layer is policy enforcement. Organizations increasingly use policy-as-code frameworks to define remediation rules programmatically. Policies can automatically prevent insecure workloads from entering production environments or enforce remediation actions when violations occur.
Examples of automated policy enforcement include:
- Blocking privileged containers
- Preventing root access
- Enforcing image signing
- Restricting dangerous Linux capabilities
- Enforcing network segmentation rules
Policy engines provide consistency across clusters and reduce human error significantly.
Another essential architectural component is runtime protection. Runtime systems monitor workload behavior continuously and detect active attacks such as:
- Privilege escalation
- Container escapes
- Unauthorized process execution
- Suspicious network communication
- Crypto mining activity
Runtime remediation systems can automatically isolate or terminate compromised workloads before attackers spread further inside the environment.
Centralized visibility is another foundational requirement. Multi-cluster Kubernetes environments generate massive amounts of telemetry data. Security teams require unified dashboards that aggregate:
- Vulnerability data
- Runtime alerts
- Compliance violations
- Audit logs
- Cluster configurations
- Remediation status
Without centralized observability, remediation operations become fragmented and inefficient.
CI/CD integration is also a major architectural component. Modern Kubernetes remediation workflows shift security earlier into development pipelines. This approach, commonly known as DevSecOps, integrates remediation directly into software delivery workflows.
Security checks now occur during:
- Code commits
- Build stages
- Container packaging
- Deployment pipelines
- Runtime operations
This prevents vulnerabilities from reaching production environments in the first place.
Another increasingly important layer is AI-assisted remediation. AI systems help prioritize vulnerabilities, identify attack patterns, reduce false positives, and recommend remediation actions automatically. In large Kubernetes environments, AI significantly improves remediation efficiency and reduces operational overhead.
Finally, validation and post-remediation monitoring complete the architecture. After remediation actions occur, organizations must verify:
- Vulnerabilities are resolved
- Workloads remain functional
- Policies are enforced correctly
- No new issues were introduced
Continuous monitoring ensures remediation actions remain effective over time.
Step-by-Step Kubernetes Remediation Workflow Implementation
Implementing a Kubernetes remediation workflow requires more than deploying security tools. Organizations must create operational processes that integrate security, development, infrastructure, and automation into a single coordinated system.
The first step is asset discovery and workload inventory management. Organizations cannot remediate what they cannot see. Security teams must continuously identify:
- Clusters
- Namespaces
- Workloads
- APIs
- Images
- Services
- Nodes
- Secrets
This inventory provides the foundation for all remediation operations.
The second step is continuous vulnerability and configuration scanning. Organizations should scan workloads across every stage of the lifecycle, including development, staging, deployment, and runtime environments.
Scanning should include:
- Container image scanning
- Kubernetes manifest analysis
- Infrastructure-as-code scanning
- Dependency analysis
- Runtime threat detection
Continuous scanning ensures vulnerabilities are identified immediately rather than during periodic audits.
The third step is contextual risk prioritization. This is one of the most important phases of the workflow because not every issue requires the same response. Effective prioritization frameworks evaluate:
- CVSS severity
- Internet exposure
- Runtime activity
- Workload sensitivity
- Exploit availability
- Compliance impact
Without prioritization, teams often waste resources on low-risk vulnerabilities while critical threats remain unresolved.
The fourth step is automated ticketing and incident orchestration. Once vulnerabilities are identified and prioritized, remediation workflows should automatically trigger actions such as:
- Creating tickets
- Assigning ownership
- Triggering notifications
- Launching automated playbooks
Automation reduces response times significantly and improves accountability.
The fifth step is containment and isolation. When runtime threats or active attacks are detected, organizations must isolate affected workloads immediately to prevent lateral movement.
Containment actions may include:
- Quarantining pods
- Blocking network communication
- Revoking credentials
- Freezing deployments
- Scaling workloads down
Fast containment is often more important than immediate patching because it limits attacker movement.
The sixth step is remediation execution. This stage includes applying patches, updating configurations, rebuilding images, or redeploying workloads.
Modern remediation workflows rely heavily on immutable infrastructure principles. Instead of patching containers directly, organizations rebuild secure images and redeploy workloads automatically.
The seventh step is validation and testing. Security teams must confirm remediation actions resolved the issue without introducing operational failures.
Validation includes:
- Re-scanning workloads
- Verifying policy compliance
- Monitoring runtime behavior
- Conducting regression testing
The final step is continuous monitoring and optimization. Kubernetes remediation is not a one-time process. Organizations must continuously improve workflows based on:
- Incident trends
- Threat intelligence
- Operational metrics
- Runtime telemetry
Metrics commonly tracked include:
- Mean time to detect (MTTD)
- Mean time to remediate (MTTR)
- Vulnerability recurrence rates
- Policy violation frequency
These metrics help organizations measure remediation maturity and improve security operations over time.
Best Practices, Challenges, and Future of Kubernetes Remediation Workflows
Implementing Kubernetes remediation workflows successfully requires both technical controls and operational discipline. Many organizations deploy scanning tools but fail to build effective remediation processes around them.
One of the most important best practices is adopting a “shift-left” security approach. Security checks should occur as early as possible in development pipelines. Detecting vulnerabilities before deployment significantly reduces remediation complexity and cost.
Another critical practice is using immutable infrastructure principles. Instead of patching running containers manually, organizations should rebuild secure images and redeploy workloads automatically. This approach improves consistency and reduces configuration drift.
Organizations should also enforce least-privilege access aggressively. Overprivileged workloads remain one of the most common Kubernetes security weaknesses. Strict RBAC policies and service account controls reduce the impact of compromised workloads significantly.
Runtime monitoring is equally important. Static scanning alone cannot detect active attacks. Runtime systems provide visibility into:
- Process execution
- Network activity
- Behavioral anomalies
- Privilege escalation attempts
Runtime-aware remediation is becoming the standard for enterprise Kubernetes security.
Network segmentation is another major best practice. Kubernetes workloads communicate constantly across clusters, making unrestricted networking dangerous. Organizations should apply Kubernetes network policies to limit lateral movement opportunities.
Automation should also extend beyond vulnerability remediation. Organizations increasingly automate:
- Compliance enforcement
- Configuration drift correction
- Secret rotation
- Certificate management
- Patch orchestration
The goal is to reduce manual operational dependencies as much as possible.
Despite these advancements, several major challenges remain.
One major challenge is remediation fatigue. Large Kubernetes environments generate enormous numbers of alerts, making prioritization difficult. Security teams often struggle to determine which issues require immediate action.
Another challenge is balancing security with operational stability. Aggressive remediation actions can disrupt production workloads if implemented incorrectly. Organizations must carefully validate automated responses to avoid outages.
Skill shortages are also a growing issue. Kubernetes remediation workflows require expertise in:
- Cloud-native infrastructure
- Security operations
- DevSecOps
- Automation engineering
- Runtime protection
Finding professionals with deep expertise across all these areas remains difficult.
Multi-cloud complexity adds another layer of operational difficulty. Different providers use different APIs, IAM systems, and networking models, making standardized remediation workflows harder to implement.
Looking ahead, Kubernetes remediation workflows are becoming increasingly AI-driven and autonomous. AI systems are already helping organizations:
- Prioritize vulnerabilities
- Detect runtime anomalies
- Recommend remediation actions
- Automate incident response
Another major trend is runtime-first security. Organizations are shifting focus from static vulnerability lists toward identifying actively exploitable runtime threats.
Policy-as-code adoption will also continue growing. Security policies are increasingly embedded directly into infrastructure pipelines and enforced automatically during deployment and runtime stages.
Additionally, Kubernetes remediation workflows are becoming more tightly integrated with platform engineering initiatives. Internal developer platforms now include built-in remediation and policy enforcement capabilities that reduce operational burden on developers while improving governance.
Conclusion
Kubernetes remediation workflows have become essential for securing modern cloud-native infrastructure. As Kubernetes environments grow more distributed, automated, and dynamic, organizations can no longer rely on manual remediation processes or isolated vulnerability scans.
Effective remediation workflows combine continuous scanning, contextual prioritization, runtime protection, automation, policy enforcement, and centralized visibility into a unified operational system. The goal is not simply to identify vulnerabilities—it is to reduce exposure quickly, consistently, and automatically across the entire Kubernetes lifecycle.
Organizations that invest in automated remediation pipelines, runtime-aware security, and DevSecOps integration will be significantly better positioned to protect their cloud-native environments against evolving threats.
The most important takeaway is this:
Modern Kubernetes security is no longer defined by how many vulnerabilities you detect—it is defined by how quickly and effectively you can remediate them before they become exploitable incidents.