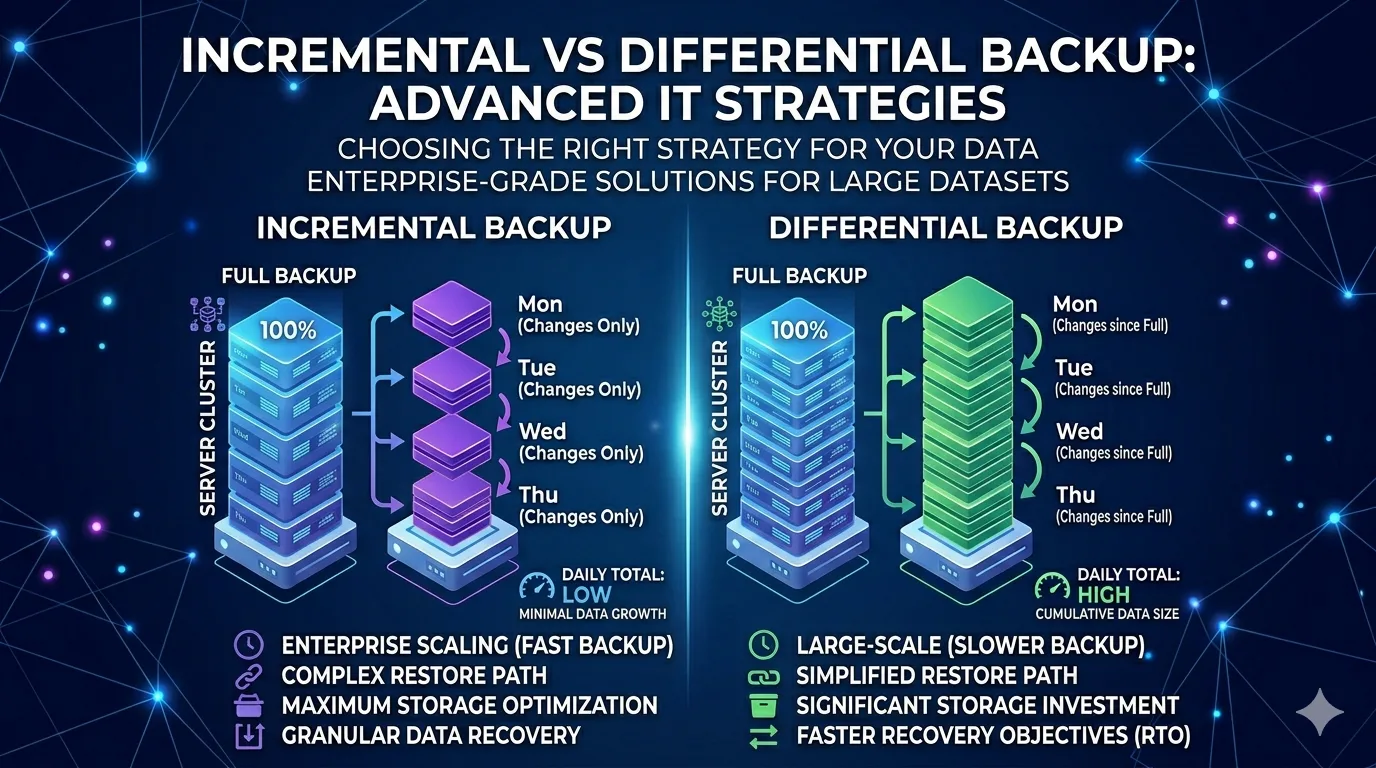
Enterprise environments require highly resilient disaster recovery protocols. Full backups capture entire datasets to provide a comprehensive architectural baseline. Executing full backups daily, however, places an unsustainable strain on network bandwidth and storage infrastructure.
Modern IT architecture demands efficient data recovery workflows. System administrators must balance resource allocation with strict Service Level Agreements (SLAs), making the choice of backup methodology a critical infrastructural decision. Two primary strategies dominate this space: incremental and differential backups. Understanding incremental vs differential backup technical nuances is essential for optimizing your disaster recovery posture.
Deep Dive into Incremental Backups
Incremental backup methodologies prioritize minimal resource consumption during the backup execution phase.
Mechanism: Tracking Granular Changes
An incremental backup identifies and stores only the block-level modifications made since the last backup operation, regardless of whether that preceding operation was a full or an incremental backup. This relies on archive bits or timestamp tracking to isolate exact delta changes.
Advantages: Storage Efficiency and Speed
This approach is highly efficient for dynamic datasets. By exclusively capturing modified blocks, incremental backups minimize the backup window and drastically reduce the storage footprint on your target network-attached storage (NAS) or storage area network (SAN).
Disadvantages: Restoration Chains and RTO
The primary bottleneck emerges during the restoration phase. To rebuild a system, the software must sequentially compile the initial full backup and every subsequent incremental backup. If a single file in that restoration chain is corrupted, the entire recovery process fails. This complexity inherently increases the Recovery Time Objective (RTO).
Ideal Scenarios for Implementation
Incremental strategies thrive in environments dealing with highly volatile, frequently changing data where strict bandwidth limits or limited storage capacities dictate operations.
Unpacking Differential Backups
Differential backups take a structurally distinct approach, prioritizing recovery speed over daily storage efficiency.
Mechanism: Tracking Against the Baseline
A differential backup captures all data modified since the last full backup. It ignores intermediate differential backups, constantly referencing the original baseline to determine which blocks require copying.
Advantages: Accelerated Restores
Because the backup payload references the baseline directly, restoration requires exactly two components: the latest full backup and the most recent differential backup. This consolidated restoration chain significantly accelerates the recovery process compared to incremental models.
Disadvantages: Storage Expansion
The backup size grows cumulatively each day until a new full backup resets the baseline. This consumes progressively more storage and extends the backup window as the week progresses. Redundant data capture is mathematically inevitable.
Optimal Performance Use Cases
Differential backups offer optimal performance for infrastructure with aggressive RTO requirements, less volatile datasets, and sufficient storage scaling capabilities to handle the cumulative data bloat.
Comparative Analysis: An Advanced Perspective
Choosing between these strategies requires evaluating exactly how they interact with enterprise-grade infrastructure.
Deduplication and Compression
Incremental backups benefit heavily from inline deduplication, as the incoming data stream is already minimal. Differential backups require aggressive target-side deduplication to mitigate the cumulative storage bloat, requiring more compute overhead on the storage appliance.
Impact on RPO and RTO
Incremental architectures favor tight Recovery Point Objectives (RPOs). Because the backups execute rapidly, administrators can schedule them hourly without disrupting production workloads. Differential architectures favor tight RTOs by minimizing the datasets required to execute a full system rebuild.
Cost Implications for Enterprise Systems
Incremental protocols reduce upfront storage hardware costs but can increase compute costs during complex, prolonged restores. Differential protocols demand higher storage provisioning, translating to higher physical or cloud-block storage expenses.
Security and Backup Chains
Validating the integrity of a lengthy incremental chain is a computationally heavy process. Both methodologies require AES-256 encryption at rest and in transit, but securing an incremental chain requires more frequent cryptographic hashing to ensure chain continuity.
Hybrid Strategies and Modern Architectures
Modern storage architectures rarely rely on a single, isolated methodology. IT teams frequently combine incremental strategies with periodic synthetic full backups, utilizing compute power on the storage appliance to automatically compile incremental chains into a fresh full backup.
Furthermore, Continuous Data Protection (CDP) and storage-level snapshot technologies augment traditional backup methods. These systems capture byte-level I/O changes in real-time, operating beneath the file system layer. Cloud-based backup solutions natively utilize these principles, tracking block-level delta changes and asynchronously replicating them across geographic availability zones to maximize redundancy.
Strategic Alignment for Business Continuity
Selecting between incremental and differential backup types dictates your organization's resilience against data loss. IT leaders must align these mechanisms with specific business continuity goals, carefully weighing storage overhead against recovery speed.
The future of data protection relies heavily on intelligent automation. Machine learning algorithms are currently being integrated into backup management platforms, allowing systems to dynamically shift between incremental and differential methodologies based on network latency, data volatility, and predictive threat modeling. Staying ahead of the curve means adopting these hybrid, automated approaches to secure your enterprise infrastructure against any eventuality.