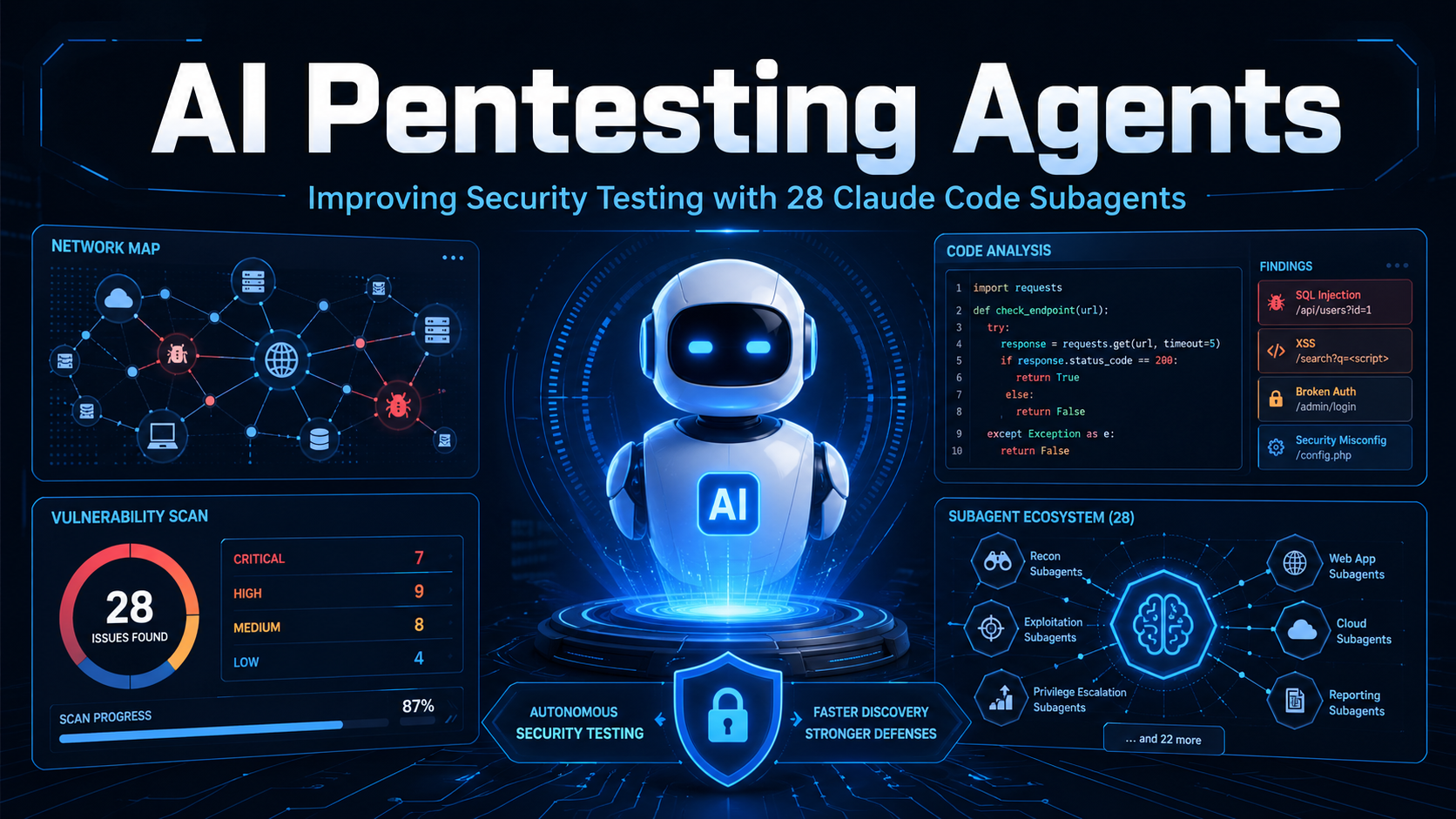
The landscape of cybersecurity is shifting from manual, labor-intensive processes to highly automated, intelligent workflows. At the heart of this transformation is the emergence of specialized AI systems like the 28 Claude Code subagents, which are designed to handle the complexities of modern penetration testing. These subagents are not just general-purpose assistants; they are domain-specific experts integrated into the Claude Code environment to perform offensive security tasks with surgical precision. By breaking down the penetration testing lifecycle into 28 distinct roles—ranging from reconnaissance to reporting—this framework allows security professionals to scale their efforts without losing the nuanced human oversight required for ethical hacking. You can find more in-depth technical details at botlearn.ai about how these agents are configured to tackle diverse attack surfaces. This modular approach ensures that each phase of a security audit is managed by a logic-driven agent optimized for that specific environment, whether it be a cloud infrastructure, a web application, or a mobile platform.
The Architecture of Specialized AI Subagents
The technical foundation of this revolution lies in the "subagent" architecture, which isolates specific tasks within their own context windows. Unlike traditional AI models that struggle with "context drift" or becoming overwhelmed by large amounts of tool output, these subagents operate independently. When a penetration tester initiates a task, the system routes the request to the most relevant specialist. For example, a subagent dedicated to web application security won't be distracted by the logs of a network scan; it focuses purely on injection vulnerabilities and business logic flaws. This isolation keeps the main conversation clean and ensures that the AI’s reasoning remains sharp. Each agent is essentially a Markdown-based configuration file that defines its personality, tool access, and specific mission, creating a cohesive "team" of experts that can be summoned on demand within a single terminal session.
Streamlining Reconnaissance and Information Gathering
The first and perhaps most critical phase of any penetration test is reconnaissance. Traditionally, this involves manually running dozens of tools like Nmap, Sublist3r, or Whois and then spending hours parsing the results to find a way in. The Claude Code subagents automate this by acting as "Recon Advisors." These agents can execute scanning tools, interpret the raw data in real-time, and suggest the next logical step based on what they find. If a subagent discovers an open port running an outdated service, it doesn’t just report the port; it cross-references the version with known vulnerability databases and flags it for the next agent in the chain. This seamless handoff between discovery and analysis significantly reduces the time it takes to map an organization’s attack surface.
Elevating Web Application and API Security
Web applications are often the primary target for attackers, and their complexity makes them difficult to secure. Within the 28-subagent framework, specific "Web Hunters" are tasked with probing these applications for common flaws like SQL injection (SQLi) and Cross-Site Scripting (XSS), as well as more complex API security issues. These agents are designed to understand the intent behind a web request, allowing them to test for business logic flaws—vulnerabilities that automated scanners often miss because they require an understanding of how the application is supposed to function. By simulating a real attacker’s thought process, these AI subagents can provide a more comprehensive look at a web app's security posture than traditional automated tools alone.
Tackling Cloud and Active Directory Complexity
As organizations move to the cloud and maintain complex internal networks, the "Active Directory Attacker" and "Cloud Security" subagents become indispensable. These specialists are trained to look for misconfigured IAM roles, exposed storage buckets, and privilege escalation paths within an enterprise environment. They can simulate lateral movement, showing how an attacker who gains a foothold in one department might eventually reach sensitive administrative controls. Because these environments are often massive and filled with noise, the AI’s ability to filter through thousands of permissions to find the one weak link is a major leap forward for red teams.
Enhancing Mobile and Wireless Security Testing
Mobile devices and wireless networks represent unique attack vectors that require specialized knowledge. The subagent framework includes experts in Android and iOS reverse engineering, as well as Wi-Fi and Bluetooth exploitation. These agents can guide a tester through the process of decompiling an app or analyzing wireless traffic to identify weak encryption or insecure data storage. By having an AI "expert" available to assist with these niche areas, security teams can perform more thorough assessments without needing to be master-level experts in every single sub-discipline of cybersecurity.
The Two-Tier Execution and Safety Model
A major concern with AI in cybersecurity is the "black box" problem—letting an AI run wild on a production network is a recipe for disaster. To solve this, the Claude Code subagents utilize a two-tier execution model. Tier 1 agents act in an advisory capacity, analyzing data and recommending commands for the human tester to run. Tier 2 agents are more autonomous; they can compose and execute commands directly, but only within a strictly defined "authorized scope." Crucially, every action a Tier 2 agent takes must be explicitly approved by the human operator. This "human-in-the-loop" design ensures that the AI provides the speed of automation while the human retains ultimate control over the safety and legality of the engagement.
Automating Documentation and Remediation Reporting
The final and often most dreaded part of a penetration test is writing the report. The "Report Generator" subagent solves this by maintaining a persistent database of findings throughout the engagement. As other agents find vulnerabilities, they log them into a SQLite-backed system. When the test is over, the reporting agent can automatically compile these findings into a professional document, complete with executive summaries, risk scores, and—most importantly—remediation guidance. This doesn’t just save time; it ensures that the "Blue Team" (the defenders) receives clear, actionable instructions on how to fix the gaps identified, ultimately leading to a stronger and more resilient security posture for the organization.