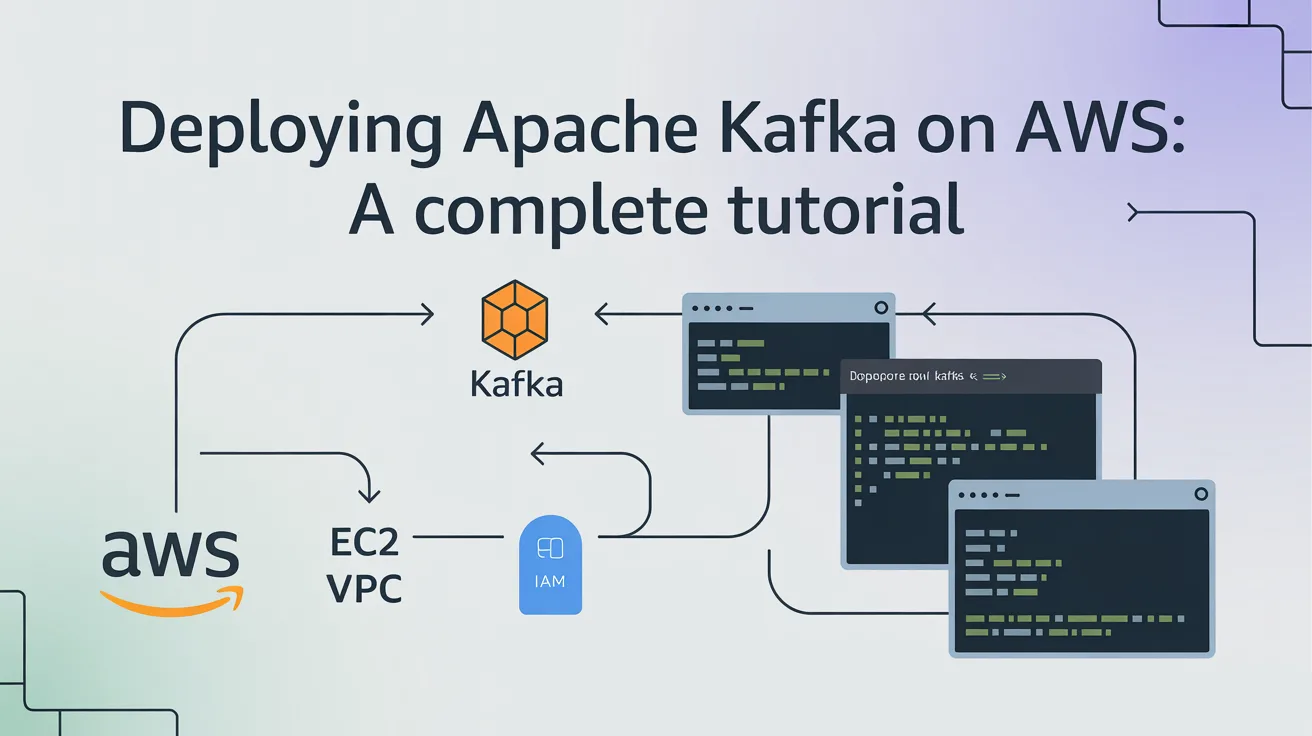
Apache Kafka has evolved into the definitive standard for event streaming, yet its infrastructure can be notoriously complex to manage. Within the AWS ecosystem, Amazon MSK (Managed Streaming for Apache Kafka) has become the preferred choice for enterprise teams, offering a balance of high-performance scaling and reduced operational overhead.
This tutorial provides a professional, step-by-step roadmap for deploying a production-ready Kafka environment on AWS using MSK, while also addressing the modern shift toward KRaft mode and IAM-based security.
1. Choosing Your Architecture
Successful deployment begins with choosing the right service model. In 2026, AWS offers several specialised flavours of Kafka:
- Amazon MSK (Provisioned): Ideal for predictable workloads where you need granular control over broker sizes (e.g., m7g instances).
- Amazon MSK Express: A high-performance tier designed for massive throughput (up to 3x standard) and sub-millisecond tail latency.
- Amazon MSK Serverless: Best for bursty or unpredictable traffic, as it scales automatically without managing broker counts.
2. Step-by-Step: Deploying Amazon MSK
Step 1: Network Preparation
Kafka requires high availability. Before creating your cluster, ensure your VPC has:
- Three Private Subnets: Distributed across three different Availability Zones (AZs).
- Security Group: Configure a group that allows inbound traffic on port 9098 (the standard port for IAM-authenticated traffic) specifically from your application servers.
Step 2: Cluster Provisioning
- Navigate to the Amazon MSK Console and select Create cluster.
- Cluster type: Choose Custom create for production environments.
Engine Version: Select 3.x+.
Strategic Tip: Transition to KRaft (Kafka Raft) mode. By 2026, the industry has largely moved away from ZooKeeper-based clusters to simplify architecture and improve metadata performance.
- Brokers: For a standard production setup, choose 2 brokers per AZ (6 total) using m7g (Graviton-based) instances for the best price-performance ratio.
Step 3: Security & Access Control
Standardise on AWS IAM Access Control. This is the most secure method because:
- It integrates natively with AWS identity policies.
- It eliminates the need to manage SASL/SCRAM secrets or TLS certificates for authentication.
- You can define granular permissions (e.g., allowing a specific Lambda function to read but not write to a topic).
3. Configuring the Client Environment
To interact with your cluster, you need a client (typically an EC2 instance or a container in the same VPC).
Install Java: Ensure you are using Java 17 or later.
Bash
sudo dnf install java-17-amazon-corretto
Download Kafka Binaries:
Bash
wget https://archive.apache.org/dist/kafka/3.6.0/kafka_2.13-3.6.0.tgz tar -xzf kafka_2.13-3.6.0.tgz
Get Bootstrap Servers: Use the AWS CLI to retrieve your cluster's connection string:
Bash
aws msk get-bootstrap-brokers --cluster-arn <YourClusterArn>
4. Production Best Practices (E-E-A-T)
- Storage Tiering: Enable MSK Tiered Storage to automatically offload older data to Amazon S3. This allows you to retain data for months or years at a fraction of the cost of EBS volumes.
- Monitoring: Set up Amazon CloudWatch alarms for UnderReplicatedPartitions. In a healthy cluster, this value should always be 0.
- Right-Sizing: Monitor the utilisation of your brokers. If usage consistently exceeds 60%, consider upgrading your broker type or adding more brokers to the cluster.
5. Summary Table: Deployment Quick-Reference
FeatureRecommended Standard (2026)BenefitOrchestrationKRaft ModeNo ZooKeeper; easier scaling.ComputeGraviton3 (m7g instances)Up to 25% better performance vs x86.AuthenticationAWS IAMNative, secret-less security.StorageTiered (S3 Integration)Infinite retention at lower costs.Conclusion
Deploying Apache Kafka Courses on AWS has shifted from a manual infrastructure hurdle to a streamlined, managed experience. By leveraging Amazon MSK with KRaft mode and IAM security, you ensure your event-driven applications are built on a foundation of authoritative stability and career-ready scalability.