Virtual Private Networks, also known as VPNs, are quite wonderful services that can be used by people to secure their online activity. Depending on the way you use this, there are different configurations that can be used for connections and different protocols to use. However, have you ever heard about a VPN concentrator, then you do not have to worry, as this guide tells you about what a VPN concentrator is and how it is used by people.
What’s a VPN concentrator?
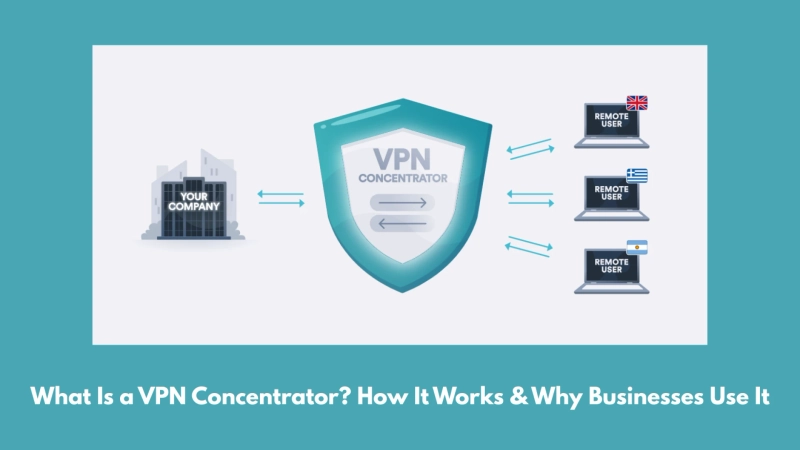
Picture it like the multitool for big company networks. It’s a special piece of hardware (sometimes just software) that keeps track of hundreds or even thousands of VPN connections all at once, right from one spot. Your personal VPN covers your phone or laptop, but a VPN concentrator is built for the whole team, everyone working remotely, all at the same time.
What does a VPN concentrator do?
The VPN concentrator creates a bunch of encrypted tunnels at once. That means everyone who connects gets a secure line straight to the main system. It acts like the brains behind the scenes, handling logins, scrambling and unscrambling data, and swapping out users’ IP addresses to keep everything private and safe. Basically, it’s what lets giant groups of people work securely from just about anywhere.
VPN concentrators serve as the primary solution for organizations that include Fortune 500 companies, government agencies, healthcare systems, and educational institutions. The organizations that operate with hundreds or thousands of remote employees use VPN concentrators to establish secure remote work capabilities.
What is the functioning of a VPN concentrator?
VPN concentrators are typically used by companies to create individual tunnels for every remote worker. These devices are used to ensure that the employee traffic is encrypted before it reaches the internal network. This allows the connection to remain secure. The concentrator is used to handle all the heavy tasks, such as authenticating users, managing encryption keys, and routing traffic safely between the internet network resources and remote devices.
You can use the website VPNeer to learn more about the working of VPN concentrators and the top concentrators that you can use.