Risks of Sharing Your Real Phone Number Online and How to Avoid It
We cannot deny that today all information is dominated by digital media, sharing personal information online has almost become an important part. However, the convenience of connecting also poses many risks, especially when sensitive details such as your real phone number are revealed. In this article, we will delve into the potential dangers associated with sharing phone numbers online and how smser.net can assist you in this process.
Risks of Sharing Your Real Phone Number Online
Sharing your real phone number online can expose you to many risks that threaten your privacy and security.
A. Privacy concerns:
Unauthorized access to personal information:
When you share your real phone number, there is a risk of unauthorized access to your personal information. This can happen through a data breach or by malicious actors exploiting vulnerabilities in online platforms.
Increased risk of identity theft:
Your phone number is often linked to many different aspects of your identity. If it falls into the wrong hands, it can significantly increase the risk of identity theft. This can lead to fraudulent activities, financial loss, and damage to your reputation.
B. Spam and unwanted calls:
Telemarketing calls:
According to statistics, online harassment and bullying are increasing significantly. That harassment and bullying doesn’t just stop on social networking sites and it also attacks through regular calls and text messages. This is done by ignorant, unscrupulous, and poorly educated people causing extremely unpleasant troubles.
Scam calls and scam attempts:
Sharing your phone number makes you vulnerable to scam calls and phishing attempts. As users get smarter, it means scammers have more sophisticated new tricks to trick individuals into revealing sensitive information, posing a serious threat to financial and personal security your.
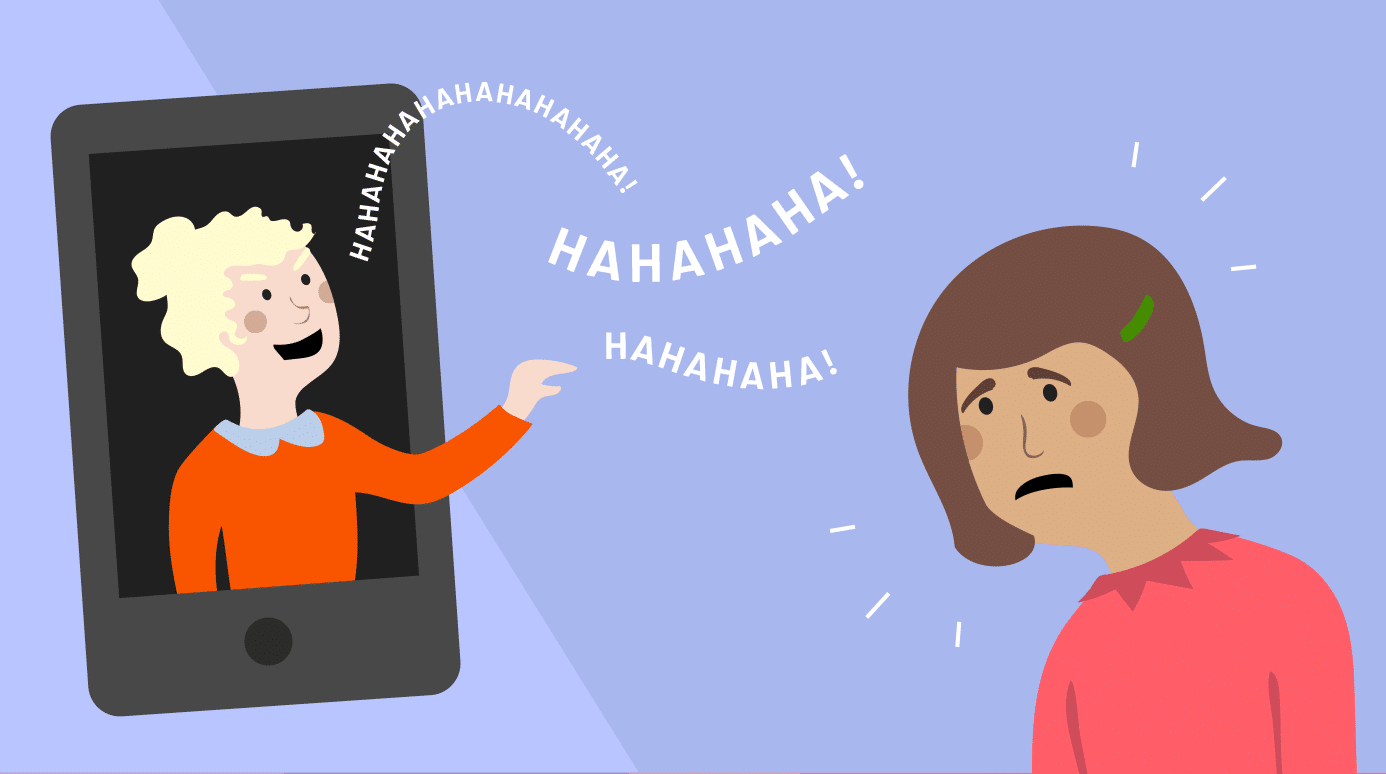
C. Exposure to cyberbullying:
Harassment via text or call:
Cyberbullies can use your phone number to harass you through text messages or calls, creating a painful and invasive experience that can be difficult to escape.
Doxxing capabilities:
Sharing your phone number online increases the risk of doxxing, in which malicious individuals publicly disclose and distribute your personal information for harmful purposes. This can have real consequences and affect your safety.
Real-Life Examples
There are countless cases of online harassment and fraud through personal phone numbers, but here I leave you with a few of the most common examples.
Example 1: A person shares their phone number on a social media platform, and it falls into the hands of a cyberbully who starts sending malicious messages and making threatening calls.
Example 2: An individual receives a call claiming to be from a government agency, demanding immediate payment for a fake debt, leading to financial loss.
Example 3: After entering their phone number on an online form, an individual starts receiving numerous telemarketing calls offering products or services.

How Phone Numbers Are Exploited:
Understanding the ways in which phone numbers are exploited sheds light on the potential vulnerabilities in the digital landscape.
A. Data Brokerage:
Selling and trading personal information:
In the world of data brokerage, phone numbers are valuable commodities. Companies known as data brokers collect and aggregate personal information, including phone numbers, and sell or trade this data to third parties. This practice raises concerns about the transparency and ethics of data handling in the digital age.
Lack of control over data dissemination:
Once your phone number enters the data brokerage ecosystem, you lose control over how it’s disseminated. It may be shared among various entities without your knowledge or consent, leading to a loss of privacy and an increased risk of your information falling into the wrong hands.
B. Social Engineering:
Manipulating individuals to disclose personal information:
Phone numbers are often exploited through social engineering tactics, where attackers manipulate individuals into willingly divulging personal information. This could involve building a false sense of trust or urgency to convince someone to share sensitive details over the phone.
Phishing attacks targeting phone numbers:
Phishing attacks, a prevalent form of cybercrime, often target phone numbers. Attackers may send fraudulent messages or emails that appear legitimate, aiming to trick individuals into providing sensitive information. This could include clicking on malicious links or sharing account credentials over the phone.
Ways to Avoid Sharing Your Real Phone Number
Adopting alternative strategies can help protect your privacy while staying connected in the online world.
A. Using receive sms online
Explanation of receive sms online service:
Receive sms online is to use a temporary or alternative phone number that can be used for specific purposes, such as registration or online communication. These numbers are not tied to a SIM card or physical location, providing an extra layer of security.
Benefits of using virtual numbers to online sms receive:
Using online sms receive offers several benefits, including increased privacy, the ability to create separate numbers for different purposes, and the option to easily change or remove virtual numbers if needed. This strategy helps individuals maintain control over their personal information.
B. Two-factor authentication (2FA)
Enhance account security without revealing actual amounts:
Two-factor authentication (2FA) is a security measure that adds an extra layer of protection to online accounts. Instead of relying solely on a password, 2FA requires an additional verification step, often involving a code sent to the mobile device. This allows you to secure your account without explicitly revealing their real phone number.
The importance of secure authentication methods:
Secure authentication methods, such as 2FA, play an important role in preventing unauthorized access to online accounts. By emphasizing the importance of these methods, you can prioritize account security without compromising the security of their real phone number.
C. Privacy policy and settings:
Review and adjust privacy settings on social media platforms:
Social media platforms often allow users to control who can access their contact information, including phone numbers. By regularly reviewing and adjusting privacy settings, individuals can limit access to their phone numbers, ensuring that only trusted contacts can see or use them this information.
Understand and enforce platform security policies:
Each online platform has its own privacy policy governing the use of personal information. You should take the time to understand these policies and, when necessary, enforce your preferences. This may include refusing to share data and reporting any violations to the platform.

Conclusion
In short, providing your real phone number on online sites will unintentionally bring a lot of trouble in your life. I hope that after reading this article you will be more aware of protecting your personal information. Oh, don’t forget to apply the solutions I analyzed above to help keep your information more secure!


